Pidgin is considered to be a fairly safe application and it’s not really open to vulnerabilities, but it seems that is not above reproach.
According to the security notice, “It was discovered that Pidgin incorrectly handled certain messages from Gadu-Gadu file relay servers. A malicious remote server or a man in the middle could use this issue to cause Pidgin to crash, resulting in a denial of service, or possibly execute arbitrary code.”
For a more detailed description of the problems, you can see Canonical’s security notification. As usual, if you are using this package, you should consider upgrading as soon as possible.
The flaws can be fixed if you upgrade your system(s) to the latest pidgin and libpurple0, and dovecot-imapd packages specific to each distribution. To apply the patch, run the Update Manager application.
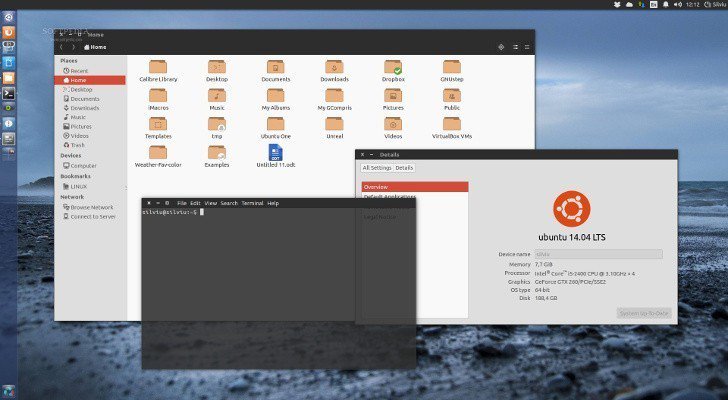
If you don’t want to use the Software Updater, you can do this from a terminal. Open a terminal and enter the following commands:
sudo apt-get update
sudo apt-get dist-upgrade
In general, a standard system update will make all the necessary changes. In order to plug the vulnerability, you need to also restart Pidgin.