To the untrained eye, the email in question will probably sound legitimate. Highlighted by the fine gents at Symantec, the spam campaign contains various clues that give away its malicious intent, starting with the email subject and ending with the attached file.
“Symantec recently uncovered a spam campaign using Heartbleed as a way to scare users into installing malware onto their computers. The email warns users that while they may have done what they can by changing their passwords on the websites they use, their computer may still be ‘infected’ with the Heartbleed bug.”
The email goes as far as to claim that if your antivirus tries to warn you, it’s because HeartBleed caused it to go insane. The campaign basically tries every trick in the book to get you to run the malicious executable hidden beneath a DOCX file.
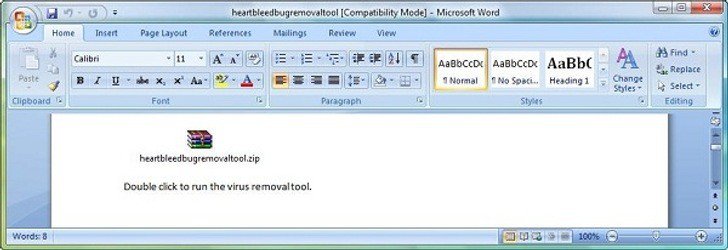
“The attached file is a docx file which may seem safer than an executable file to users. However, once the docx file is opened the user is presented with an encrypted zip file. Once the user extracts the zip file, they will find the malicious heartbleedbugremovaltool.exe file inside,” Symantec explains.
Whoever gets tricked into running the program will unknowingly have downloaded a keylogger that records keystrokes (containing your passwords, credit card info, and whatever you regularly type on your computer), takes screenshots, and sends this information to a free hosted email provider.
“This type of social engineering targets users who may not have enough technical knowledge to know that the Heartbleed bug is not malware and that there is no possibility of it infecting computers. The email uses social and scare tactics to lure users into opening the attached file,” Symantec warns.
The security firm urges users to be skeptical whenever faced with emails that request personal information as well as emails containing attachments with instructions to execute the bundled program.
“Users should also avoid clicking on links in suspicious messages,” according to the Mountain View-based security company.
The firm adds, “Symantec detects this malware as Trojan.Dropper and detects the downloaded malicious file as Infostealer [while the] Symantec.cloud Skeptic heuristics engine is blocking this campaign and detecting it as Trojan.Gen.”