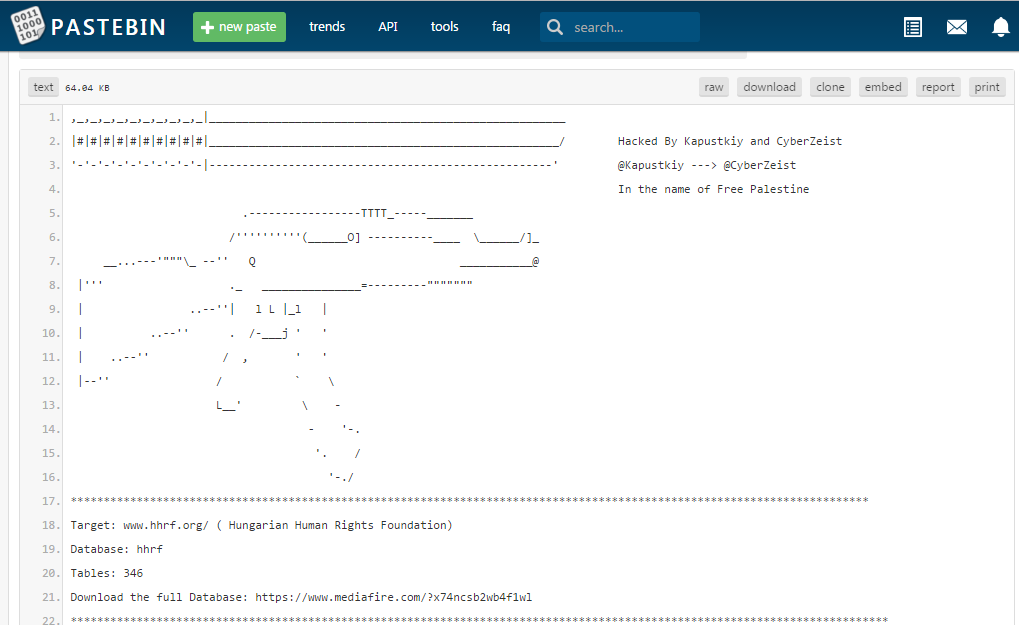
The Hungarian Human Rights Foundation website was hacked with SQL injection by Kapustkiy and CyberZeist. They managed to get access to over 20,000 accounts by this data breach.
Kapustkiy told that the data breach was possible with a SQL injection, which provided him with access to databases that included thousands of accounts and personal information which includes phone numbers and home addresses. However some of the accounts accessed were related to the US government (using the @state.gov suffix).
According to the Softpedia reporters, he told them that he already contacted them to report the flaw and the security team said it would investigate the breach, but for the moment, the website still appears to be up and running.
This is not the first time, Kapustkiy found several other vulnerabilities in high-profile websites, including one that allowed him to infiltrate into an Italian government website and access details of thousands of users.
As usual Kapustkiy decided to leak only part of the accounts and give IT administrators more time to fix this issue. However now the website if down with a message “Down For Maintenance. Sorry for the inconvenience, but we are performing a maintenance at the moment.We will be back online shortly!”