So what is this phishing tool all about?
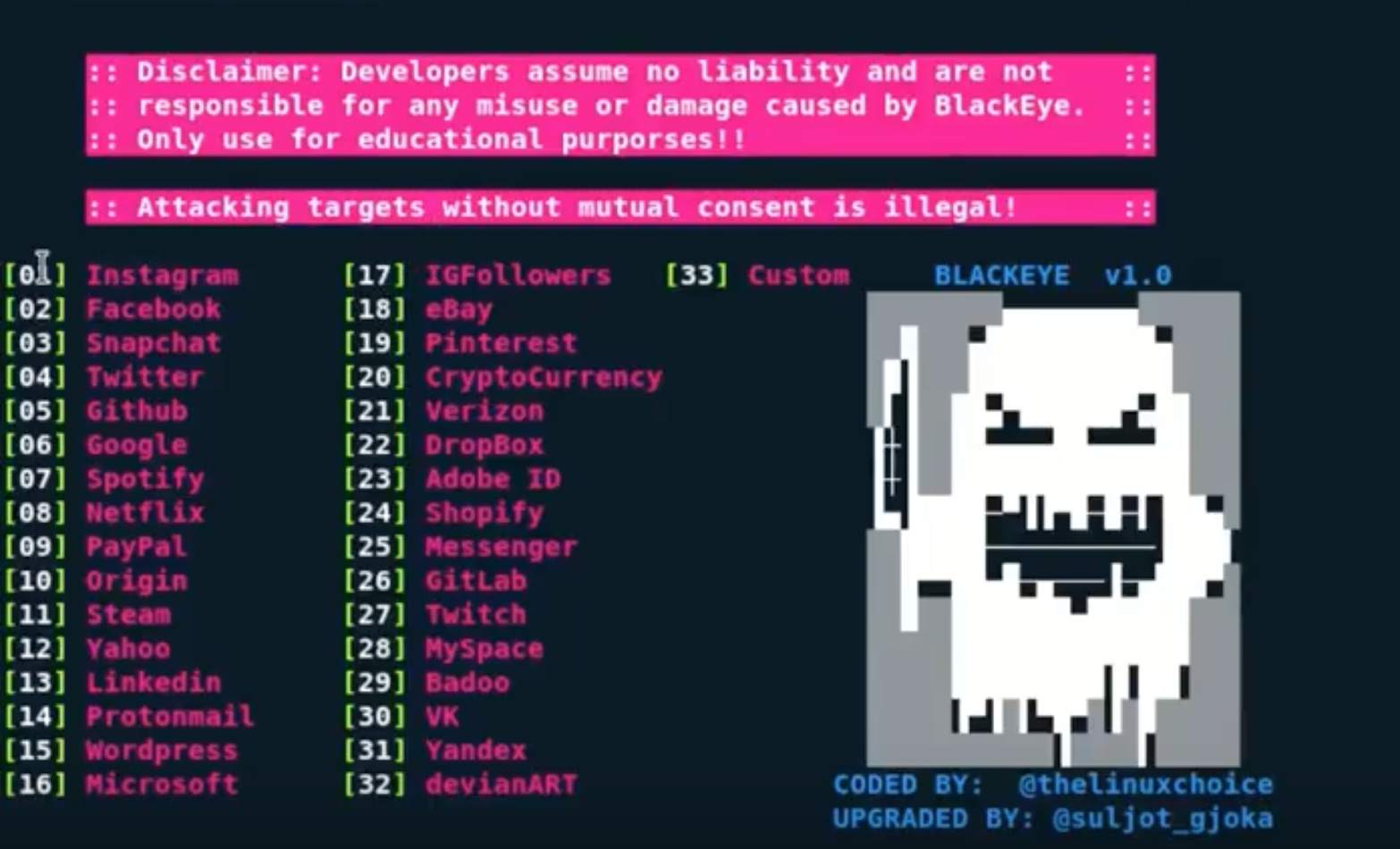
Blackeye is tool scripted in shell to perform phishing attack inside and outside LAN combined with ngrok.
It can be used for social engineering related pen testing jobs, it may also come in handy for red teaming when trying to gather passwords that could be used elsewhere.
What features does it offer?
Blackeye is the most complete phishing tool yet with 37 web templates +1 customizable. It can collect IP and location information just by clicking the link.
– Supports mobile version
– The tool has arm support
– Supports templates of some websites that are hard to clone and unsupported by other tools
How can I install it
git clone https://github.com/whiteeagle0/blackeye cd blackeye bash blackeye.sh
Is the tool actively supported
At the time of writing Blackeye is actively supported, the team are also open to suggestions.
Any suggestion about the tool or any website can be made by contacting @suljot_gjoka on Instagram.
What Bunny rating does it get?
Blackeye is a fantastic, easy to use tool which does exactly what it says on the tin. As a result we have decided to give this tool a very respectable rating of 4/5 bunnies.




Want to learn more about ethical hacking?
We have a networking hacking course that is of a similar level to OSCP, get an exclusive 95% discount HERE
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.