Social Mapper is an open source tool that searches for profile information from social media sites, such as Facebook, Instagram, LinkedIn, Google+, Vkontakte and microblogging websites like Weibo and Douban. The tool uses names and photos as input to scan social media profiles of the people on mass. Target names and photos can be provided to the tool via csv file containing target names and urls of the target photos, or it can be a folder containing named images. It takes approximately 60-70 seconds to scan one profile based on provided names and photos.
How to Install Social Mapper
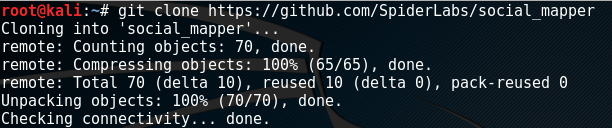
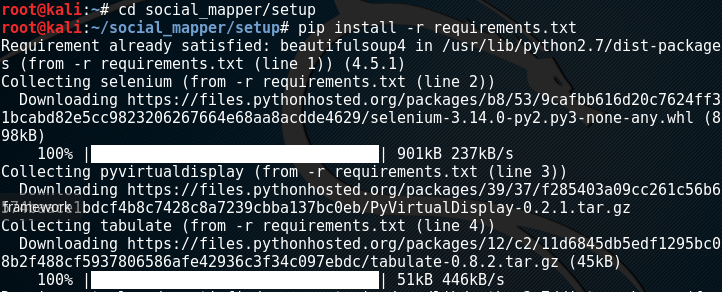
Social Mapper is written in Python and runs on Linux, Windows, and Mac. Before installing Social Mapper, some pre-requisites need to be fulfilled. These include installation of Selenium, Geckodriver, and latest version of Firefox. After that, Social Mapper can be installed by cloning the tool from Github repository using the following commands.
git clone https://github.com/SpiderLabs/social_mapper cd social_mapper/setup pip install -r requirements.txt
Running the Tool
After installing Social Mapper, it can be set into action by running the social_mapper.py file with target information and target social media site. The basic syntax of the command is as follows.
social_mapper.py -f <input format> -i <input type > -m <mode> –<target media>
Here the –i argument represents the input provided to the tool. We can provide the tool a specific name, a csv file containing target information, imagefolder, or social mapper html file. The –f specify the format of the input provided to the tool. It can be ‘social mapper’, a ‘name’, ‘csv’, or ‘imagefolder’. The –m represents the mode. The mode can be set as ‘fast’ or ‘accurate’ depending on the requirement. Finally we provide social media website information to the tool. The tool accepts –a argument as ‘select all social media’. We can also provide specific social media sites as well. Following is a list of the abbreviations that can be fed into Social Mapper to gather information about targeted users.
-a : Selects all
-fb: Check Facebook
-tw: Check Twitter
-ig: Check Instagram
-l,: Check LinkedIn
-gp: Check GooglePlus
-vk: Check VKontakte
-wb: Check Weibo
-db: Check Douban
Following is an example command that aims to find the information about specific users on facebook and twitter. The tool uses the ‘imagefolder’ format with a folder name called ‘targetusers’. The command runs in fast mode. In fast mode, the tool skips the secondary scan results after finding the first potential match of the target user.
python social_mapper.py -f imagefolder -i ./mytargets -m fast -fb -tw
The tool allows some optional parameters to use in the command to fine tune the search results. For example, we can instruct the tool to fetch results on the basis of ‘loose’, ‘standard’, ‘strict’, or ‘super strict’ policy by adding –t parameter to the command. If the threshold is set to ‘loose’, the tool finds more matching results with less accuracy. Similarly, the ‘strict’ or ‘super strict’ threshold will produce more accurate results. Following is an example command with strict threshold policy. The command runs the tool in accurate mode by searching the target users on all supported social media websites.
python social_mapper.py -f imagefolder -i ./mytargets -m accurate -a -t strict
Overall, the tool would be great for red team engagements, such as gathering information automatically about targeted social media accounts.
What Bunny rating does it get?
Social Mapper makes information gathering work easy by automating the process. Troubleshooting can be a problem for many when social media sites update their page formats and class names. As a result we have decided to give this tool an awesome rating of 4 out of 5 bunnies.




Want to learn more about ethical hacking?
We have a networking hacking course that is of a similar level to OSCP, get an exclusive 95% discount HERE
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

