Trape is a tool written in python that can aid in tracking a client after utilising a phishing attack. When a victim clicks on the phishing url, the tool captures the client victim ip address, location, and sessions of the some popular web services. Some well-known supported web services Amazon, Dropbox, Facebook, Instagram, Gmail, Tumblr, and Reddit. The captured results can be seen through the dashboard in a web browser.
Installation of the Tool
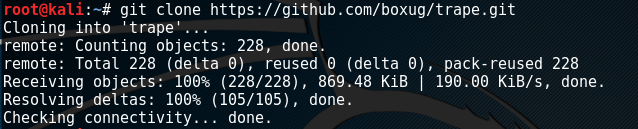
Trape can be installed by cloning the Github repository using the following commands.
git clone https://github.com/boxug/trape.git
Once the tool is installed, the required libraries can be installed using the following commands.
cd trape pip install -r requirements.txt
Let’s Have a Look Into The Tool
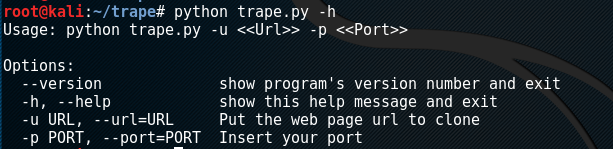
Once the tool and the required libraries are successfully installed, Trape can be set into action using the following command.
python trape.py -h
The command not only starts the tool but also provides the list of the parameters that can be set as an argument in the commands.
As mentioned earlier, Trape works on the principle of first utilising a phishing attack. A URL needs to be cloned and shared in order to trap the client victim. The cloned URL can be obtained using the following command format.
python trape.py --url <url to be cloned here> --port <port number here>
For the sake of demonstration, we can clone google.com using the port number 80 on a local host. This can be achieved using the following command.
python trape.py --url https://google.com --port 80
The above command generates three parameters, namely: phishing url, control panel url to track the victims, and a pass-phrase to log into the control panel.
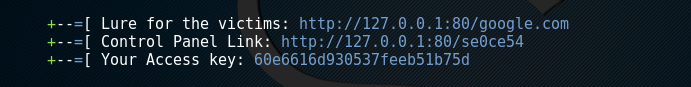
After generating the lure url , it can be shared with the victim through email or any other appropriate method. The tool waits for the victim to click on the lure url. The results are saved into Trape dashboard that can be accessed using the control panel link and generated access key.
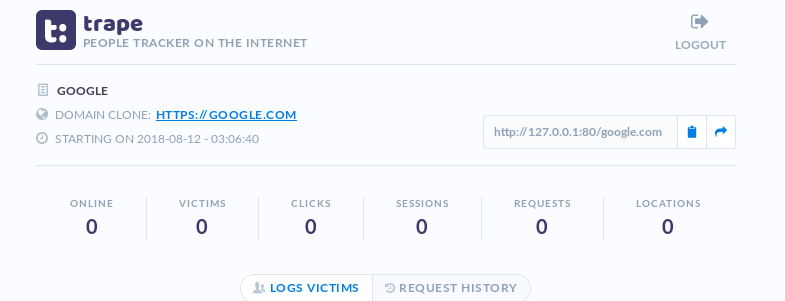
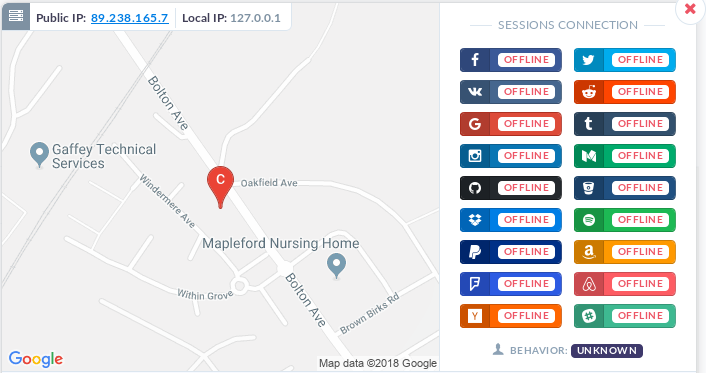
Once the victim clicks on the url, Trape captures the victim’s IP address, location, and any running session in the victim’s web browser.
What Bunny rating does it get?
The tool does not require any hard core programming to run. The tracking results are quick and accurate. Sessions are captured correctly. The tool works in real time. Everything is tracked through the web browser. As a result we have decided to give this tool an awesome rating of 4 out of 5 bunnies.




Want to learn more about ethical hacking?
We have a networking hacking course that is of a similar level to OSCP, get an exclusive 95% discount HERE
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

