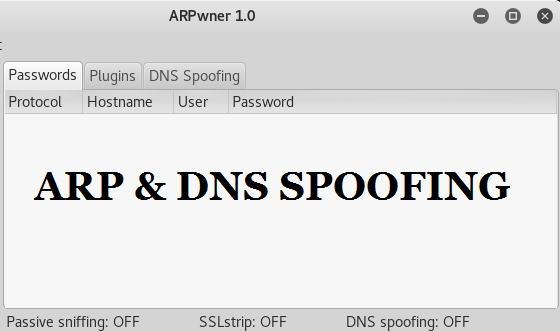
ARPwner is a GUI based tool that can perform tasks like ARP and DNS spoofing. Through ARP and DNS spoofing, the attackers can steal sensitive information by eavesdropping on the network. Address Resolution Protocol, simply called ARP, is a communication protocol that is used to map IP addresses to physical addresses, e.g MAC address of the computer systems and devices in the local network. ARP uses a table called ARP cache to maintain the correlation between the IP addresses and the MAC addresses of the local network devices. ARPwner manipulates the cache by sending the spoofed ARP messages on the local network to correlate the MAC address of the attacker’s machine with the IP address of the target machine, usually the default gateway. With that step, the entire traffic passes through the attacker’s machine. In this way, any internet traffic meant for other machines in the network can be analyzed by the attacker. The attacker can also target the IP address of a specific user machine to refine the incoming traffic. Similarly, in DNS spoofing, the DNS cache is manipulated with fake entries.
How to Install ARPwner
ARPwner requires pypcap module to operate. The pypcap can be installed as follows.
apt-get install python-pypcap
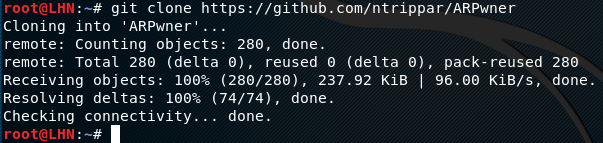
The ARPwner setup files can be downloaded by cloning the github repository as follows.
git clone https://github.com/ntrippar/ARPwner
How ARPwner Works
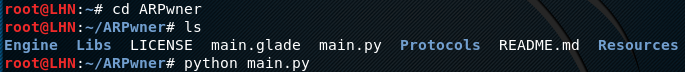
After installation, move to the ARPwner directory to run the main.py file using the following commands.
cd ARPwner python main.py
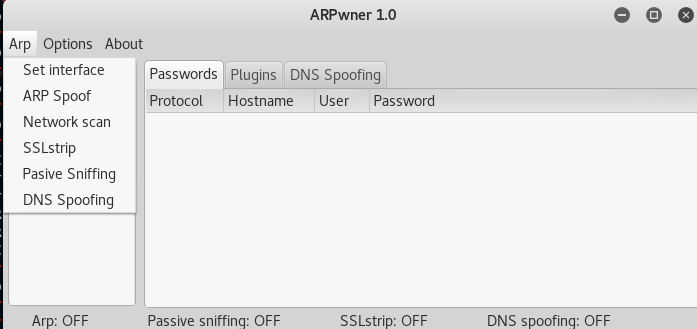
This will open the ARPwner user interface as shown in the following screenshot.
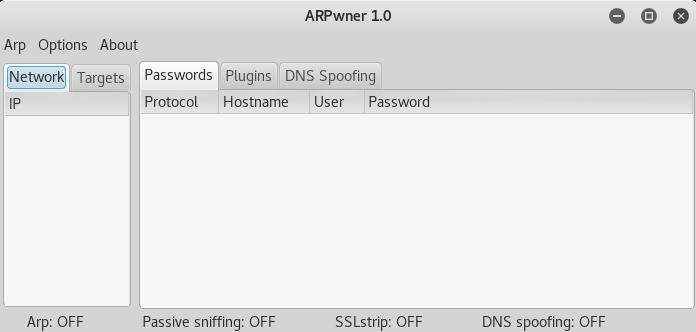
The tool is loaded with different plugins that can log account details running under different protocols, such as HTTP, FTP, IRC, IMAP, NNTP, SMTP, POP3, and TELNET. We can enable or disable any of the available plugins to collect data according to the goals.
To start the ARP or DNS spoofing, select the target interface listed under the ‘ARP’ tab. In our case, it is ‘eth0’. The next step is to scan the network. This can be achieved by providing the IP address range. Once the IP address range is provided, the tool lists all the available online devices in the local network. Any IP address can be added to the ‘Target’ list to intercept the traffic, such as password credentials of specific services accessed by the user during the sniffing process. The ARP and DNS spoofing options can be set ON and OFF by just clicking the options from the ‘ARP’ tab.
What Bunny rating does it get?
Overall, the tool is very handy to collect useful information by monitoring the local network traffic. The tool is not only capable of spoofing the network, but also utilises SSL mitigations by using SSLStrip, as a result we will be awarding this tool a rating of 4 out of 5 bunnies.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.