A newly discovered ransomware strain applies the concept of multi-threading to encrypt files and also log and steal keystrokes of victims. The new ransomware has been named Virobot and has no previous ties to any previous ransomware trees according to the cybersecurity firm Trend Micro who found the threat last week.
How is the ransomware encrypting data?
The ransomware has been using the same modus operandi which is similar to all previous ransomware on the market, the current infection has also been used for spam emails known as malspam , whereby a user is tricked into downloading and running ransomware attached to email documents. The ransomware manifests by generating a random encryption and decryption key and also sends remote commands to a control centre (C&C) server.
The encryption process relies on the RSA encryption scheme, Virobot will target files with following extensions: TXT, DOC, DOCX, XLS, XLSX, PPT, PPTX, ODT, JPG, PNG, CSV, SQL, MDB, SLN, PHP, ASP, ASPX, HTML, XML, PSD, PDF, and SWP.
Once the encryption process is completed the Virobot shows a note on the user’s screen which is written in French, despite mostly people from the US having been targeted so far.
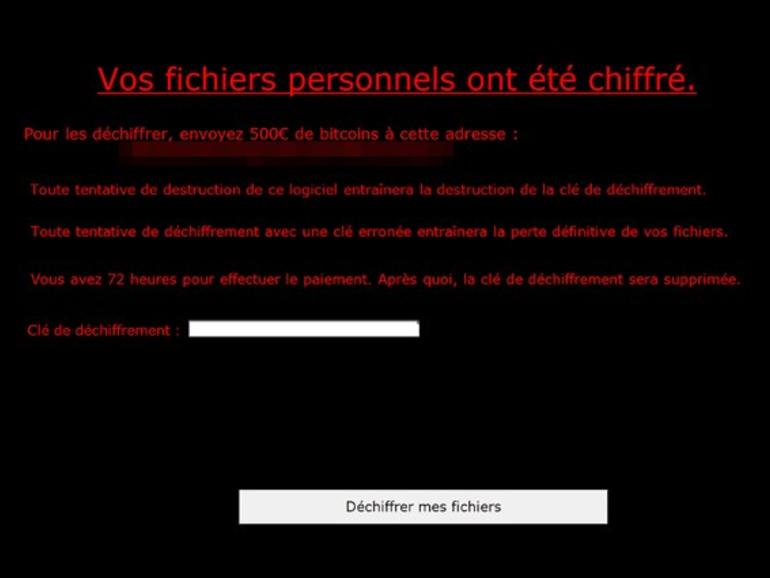
According to Trend Micro, the ransomware note is more than enough to determine if the user has been affected by the Virobot ransomware. Malware strains such as MyteryBot, LokiBot, Rakhni or XBash have been often categorised with multi-functional features hence Virobot has been pigeon-holed as a Botnet.
Take your time to comment on this article.
