Diagnostic handheld medical devices provide a convenient means to patients for monitoring their health conditions. To ease the lives of the patients, Roche has produced a range of medical diagnostic devices to check blood glucose levels and blood pressure, etc. However, as discovered recently, these devices house several security flaws. The ICS-CERT warns patients and the healthcare industry to remain careful while using these diagnostic point-of-care devices.
Vulnerabilities Found In Roche POC Handheld Medical Devices
As revealed in the advisory published by the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT), the Roche POC handheld medical devices exhibit some serious security vulnerabilities. Describing the impact of these flaws, the ICS-CERT stated in their advisory,
“Successful exploitation of these vulnerabilities could allow an attacker to gain unauthorized access to modify system settings or execute arbitrary code.”
Reportedly, as much as five different vulnerabilities affect Roche point of care handheld medical devices. The flaws include improper authentication (CVE-2018-18561), OS command injection (CVE-2018-18562), unrestricted upload of file with dangerous type (CVE-2018-18563), and improper access control (CVE-2018-18564 and CVE-2018-18565). These vulnerabilities have attained medium to high severity ratings with CVSS base scores ranging between 6.5 and 8.3.
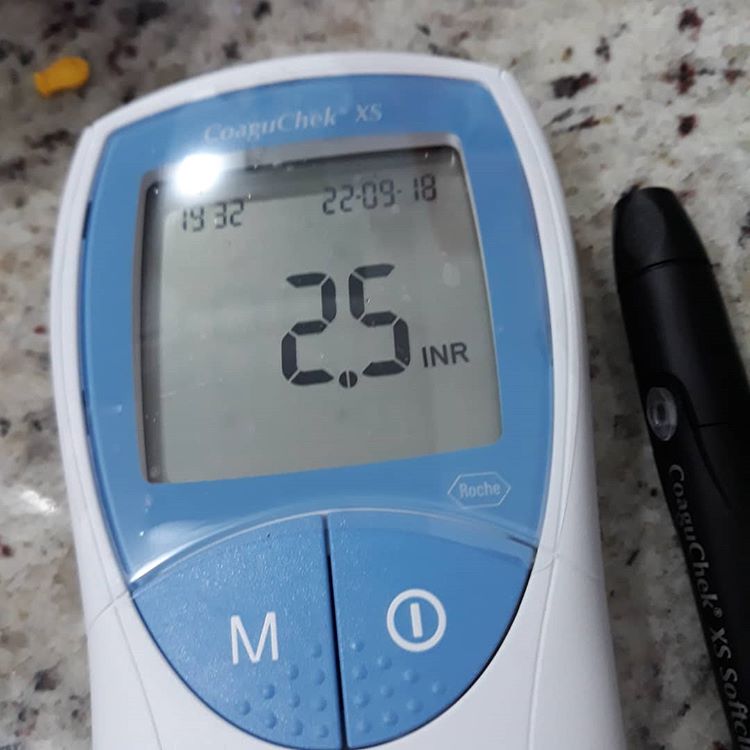
The affected Roche devices include “Accu-Chek Inform II, CoaguChek Pro II/XS Plus/XS Pro, cobas h 232 POC” and the “related base units (BU), base unit hubs and handheld base units (HBU).” Not all vulnerabilities affect all devices collectively, rather each of these affected devices may exhibit one or more of these vulnerabilities.
Fortunately, ISC-CERT confirms no public exploits, yet.
“No known public exploits specifically target these vulnerabilities.”
Recommendations For Mitigation
A researcher from medical device security firm Medigate, Niv Yehezkel, has discovered these vulnerabilities. He then duly reported the security flaws to Roche. For now, no software fixes are available by the vendors. However, Roche has certainly recommended some strategies to mitigate the flaws. These include,
- Limiting access to the devices and enabling device security features
- Ensure adequate protection of connected endpoints against unauthorized or malicious software
- Protection of non-connected devices from unauthorized access
- Vigilant monitoring of system and network infrastructure
- Prompt reporting of a “suspected compromise” to the authorities
The National Cybersecurity and Communications Integration Center’s (NCCIC) recommends users to limit internet access to the devices and systems to avoid network exposure. Moreover, they also suggest using firewalls to secure remote devices and local system networks.