BleepingComputer recently exposed a Ransomware variant called JungleSec which affects Linux servers through the IPMI (Intelligent Platform Management Interface). The threat actors targeted unsecured IPMIs to remotely access and operate the victim’s system
The Attack
The threat actors first locate systems without secure IPMIs and then gain access through the default password. Hackers can then control and operate the computer. Next, they reboot the system into a single-user mode. Finally, the files are encrypted and the user is directed towards a file named ENCRYPTED.md, which is a demand note.
This note demands 0.3 Bitcoin from the affected system owners, in order to decrypt the data. The demand note warns the computer owners against using Brute Force or other methods to regain access. In fact, the message goes on to state that any change in the bytes indicating such attempts, would result in the permanent loss of the encrypted data.
According to reports, certain victims made the Bitcoin payment, but did not receive any decryption key.
The Solution
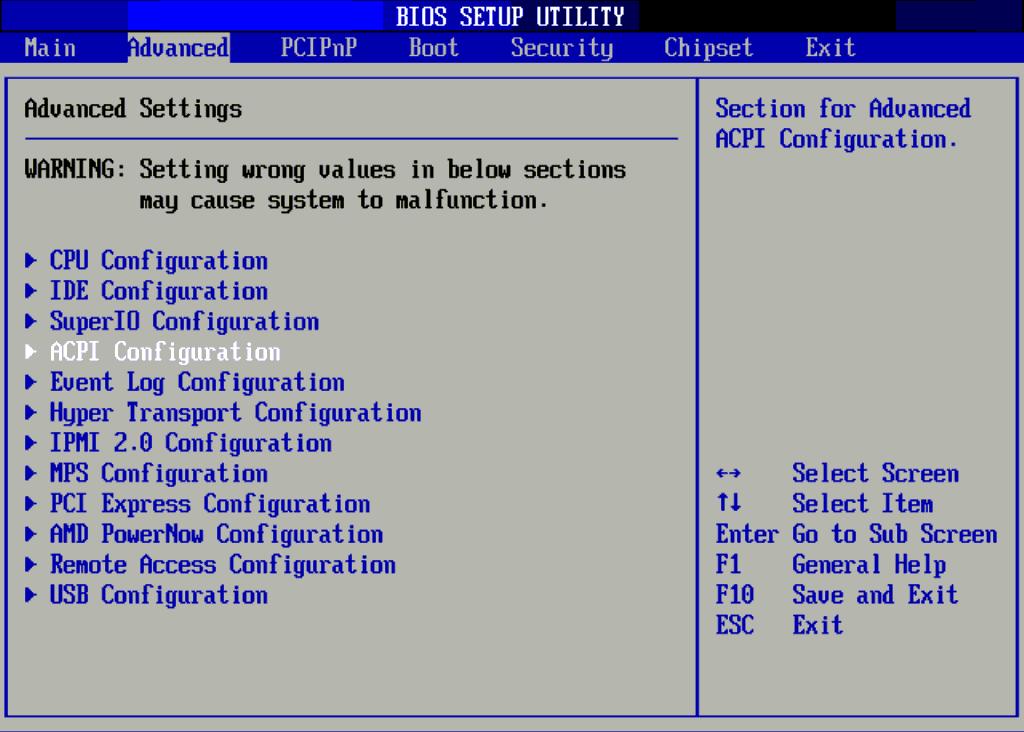
The IPMI Remote Console is a standard interface that permits authorised access to the system’s hardware. This tool is extremely useful to operate a server remotely.
However, JungleSec is only a concern for those using the IPMI default password. The best prevention against the JungleSec Ransomware attack is to simply reset your IPMI password to a something more secure, alternatively consider disabling/restricting if not required.