With Sherlock you can search across a vast number of social platforms for a username. This is useful for information gathering purposes, if you want to perform a sophisticated social engineering attack against a specific target or if you want to test if a password has been used in another platform by the same user.
Installing Sherlock
First you need to clone the repository from Github.
git clone https://github.com/TheYahya/sherlock.git
Sherlock is based on python3 so you need to install it first if you don’t have it. After that run the command below to install all the missing dependencies.
pip3 install -r requirements.txt
Running Sherlock
So let’s see what the script can do for us.
python3 sherlock.py -h

We can see a pretty basic interface. You can rank the websites by popularity, run the script through tor or another proxy for anonymity, load data from a json file and more. In our example, we will use some basic options, only. It is very easy to use. Just type the username you want to search. Let’s see what results the script gives us.
python3 sherlock.py [username]
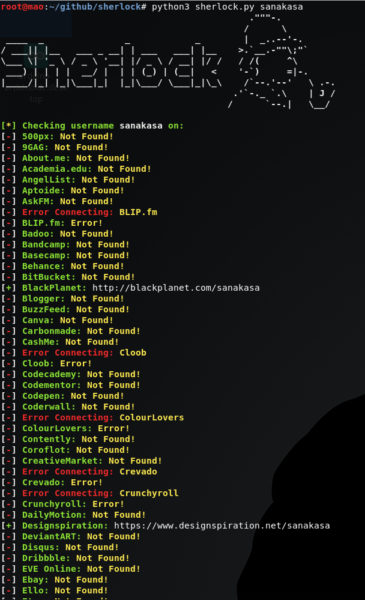
We got all the results we wanted. There are some errors but it is no big deal. Check the results manually after that.
What bunny rating does it get?
Sherlock is pretty basic and an easy to use script. The data you get can be pretty handy in the information gathering phase. It is also very fast. I got around 50 different sites in under a minute. All in all, great tool, I’m giving it 4 out of 5 bunnies.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

