Thousands of Linksys smart routers around the world can leak user data to hackers. According to a researcher, a vulnerability existing in different models of Linksys Smart WiFi routers around the world makes the users vulnerable to hacks. What’s upsetting here is that the vendor does not currently consider the problem worthy of a fix.
Linksys Smart WiFi Routers Vulnerability
Reportedly, a researcher Troy Mursch has discovered a serious vulnerability affecting various models of Linksys Smart WiFi routers. Explaining his findings in a blog post, Mursch revealed that the vulnerability can disclose sensitive user information to a potential attacker upon an exploit.
We’ve discovered a persistent flaw affecting Linksys Smart Wi-Fi routers that allows unauthenticated remote access to sensitive information.
An attacker with even little technical knowledge can exploit the vulnerability without requiring authentication. The exploit is pretty simple. An attacker merely has to visit the developer console upon after opening the router’s public IP address in the web browser. Then scrolling down to the JNAP will reveal the details.
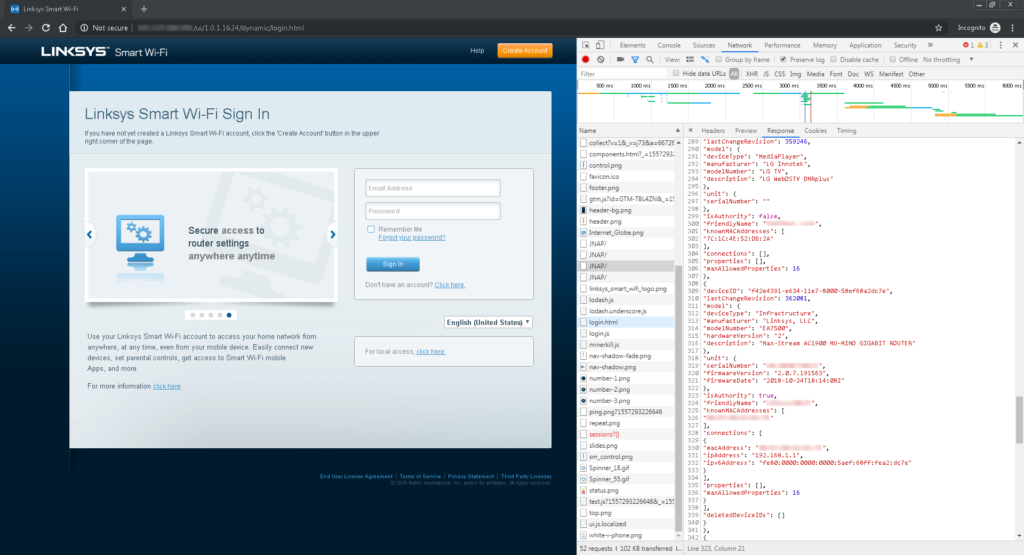
According to Mursch, as much as 25,617 routers are exploitable through this vulnerability. The leaked information may include device names, operating system information, and complete historical record of MAC addresses of devices ever connected. Whereas, in some cases, the exposed information includes additional logs, such as device type, model number, manufacturer information, a description, and system data such as WAN settings, firmware update settings, firewall status, and DDNS settings.
A complete list of devices actively leaking the information is available on this link.
Vendor Refused A Fix
While discussing the risks associated with this flaw, Mursch stated,
This information allows attackers to gain visibility inside your home or business network, enabling them to conduct targeted attacks.
The exploit can be worst in case of devices with default admin credentials. This includes almost everything from accessing the SSID credentials to hijacking web traffic and targeting devices behind the router. A potential attacker can scan for such devices via the vulnerability discovered.
Ironically, the vendors do not deem this vulnerability worth a patch. Allegedly, they closed the researcher’s report with a “Not applicable / Won’t fix” status.
Unfortunately, there seems no direct workaround either to mitigate the flaw. The users of some models can, however, consider using a third-party firmware.
Most (but not all) models have the option of using third-party firmware, such as OpenWrt, that can disable remote access and prevent the leak of sensitive information.
Take your time to comment on this article.

