Some malware campaigns seemingly never stop, rather they keep coming back again and again to prey on users. One such malware campaign involving fake jQuery has returned. This fake jQuery campaign now runs for ad fraud schemes and malvertising.
Fake JQuery Campaign For Ad Fraud
Researchers from Malwarebytes have spotted another fake jQuery campaign in the wild. The fake jQuery campaign that dates back to 2016, has once again gained momentum. Nonetheless, this time, the campaign aims at malvertising and ad fraud.
Elaborating on their findings in a blog post, the researchers stated that the payload here focuses at monetizing through ads.
The matter caught the attention of Malwarebytes after another researcher with alias ‘Placebo’ highlighted it in his tweet.
Seams the fake jquery campaign is back.https://t.co/fgS2keRGHA
I have not seen them after they were exposed by @gwillem and @unmaskparasites late 2018IOC’s
16js[.]org
22js[.]org
12js[.]org
wp11[.]org
lib0[.]org
16lib[.]org
12lib[.]org— Placebo (@PlaceboRulez) June 20, 2019
By searching the domains mentioned in this tweet on PublicWWW, the researchers could find thousands of domains infected with malicious script. When LHN attempted to cross-check this claim, we could also see at least over 1000 domains running the scripts for every domain listed by Placebo. The least results were found for “lib0[.]org” only, which were made up of a few hundred.
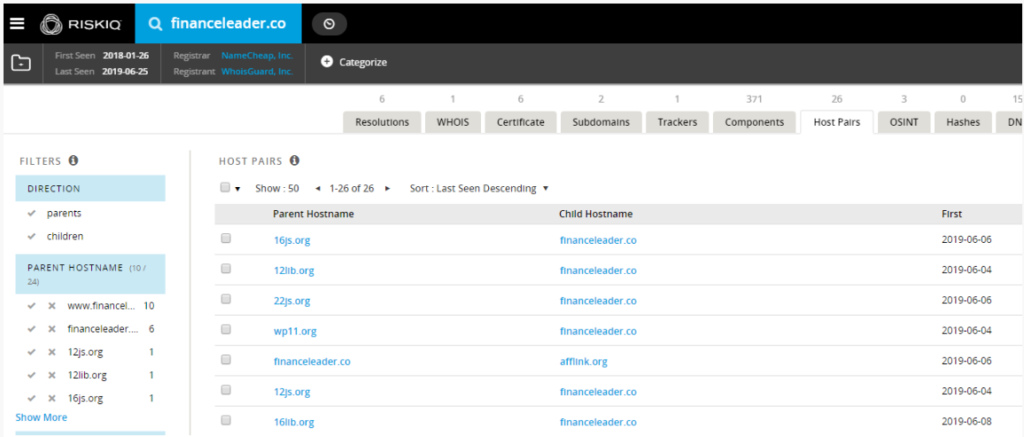
Digging further into the matter further Malwarebytes to establish that the fake jQuery domains basically redirect to other websites. They could see “12js.org” redirecting to financeleader[.]co, to which other fake domains also redirect.
Source: Malwarebytes
However, if someone tries to directly visit the malicious website “financeleader[.]co”, the user will not succeed. The link redirects to Google.com, as Malwarebytes explained and LHN can verify.
Even if a visitor reaches the malicious domain with special identifiers via desktop, the user would only see a bogus website when on a US IP address. With a non-US IP address, the link would redirect to a site advertising VPNs. This depicts some kind of geotargeting behind this campaign.
Upon further research, they could also see another domain “afflink[.]org”, besides “financeleader[.]org”, as redirect link.
Mobile Phone Users Are Main Targets
According to Malwarebytes, the main target of this campaign seems mobile phone users. Where the payload will display full-screen ads on devices at regular intervals.
Explaining about this behavior, the researchers stated,
Once we switch to a mobile User-Agent and Android in particular, we can see a lot more activity and a variety of redirects.
In one case, when visiting the site on an Android phone, the researchers could see a malicious adult app asking for download. Upon analysis, this malicious app was found to generate full-screen ads at intervals.
While the researchers could not precisely determine the scale of this malware campaign for now, they fear that it will trigger massive ad fraud.
We weren’t able to get an idea of the scale at play, especially considering that the domain initiating the redirects really only became active in late May. However, given the number of websites that have been compromised, this campaign is quite likely funneling a significant amount of traffic leading to ad fraud.
Mobile phone users must stay vigilant when browsing different sites and downloading apps. Moreover, they will benefit from using a robust antimalware app running on their devices.
Let us know your thoughts in the comments.

