Ffuf – Fuzz Faster U Fool is a great tool used for fuzzing. It has become really popular lately with bug bounty hunters. Ffuf is used for fuzzing Get and Post data but can also be used for finding hidden files, directories or subdomains.
Installation and usage
- Clone the github repository and change the current directory
- Install golang
- Run the script with the FUZZ word, url and a wordlist at least

On Kali you can easily install golang:
apt-get install golang
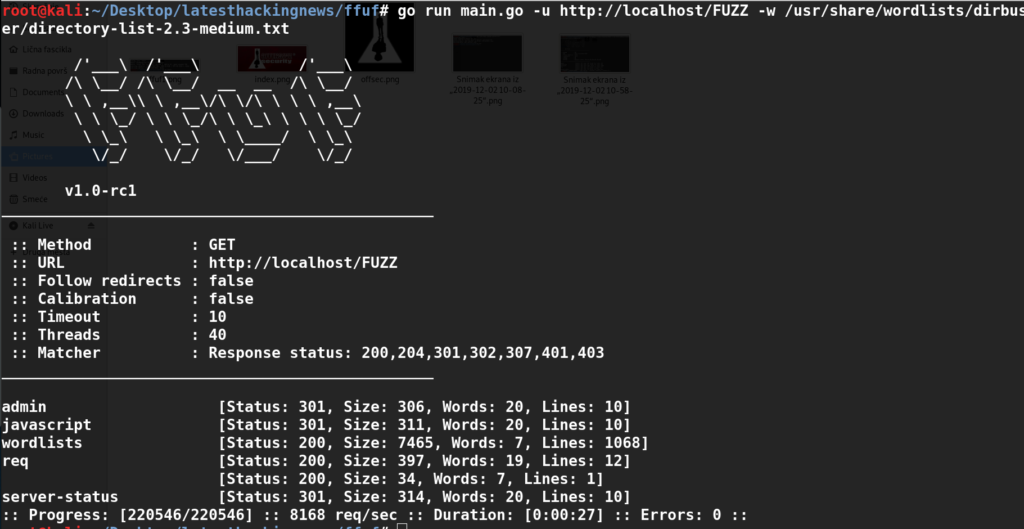
Then you can run a directory discovery which finishes the whole 200k wordlists under 30 seconds which is an impressive performance:
go run main.go -u http://localhost/FUZZ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
The tool is also great when you have to test for vulnerabilities: sqli, xss, command injection, ldap injection, nosqli, etc. For example if you come across a search get parameter you could use this command to test for sqli (if you expect a different response length where you get a sql error, opposed to the response where the parameter is just invalid):
ffuf -w sqli.txt -u https://vitim/script.php?id=FUZZ -fs <response_length>What bunny rating does it get?
Pros
- ffuf is probably the fastest web fuzzer
- it has a lot of really useful options for parameters and filtering out the response
Cons
- In some cases it can miss results if the threads and filtering are not properly set up, so it boils down to trial and error which is a small con for any fuzzer
Based on these pros and cons I will award this tool with 5/5 bunnies:





Want To Learn More About Ethical Hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.