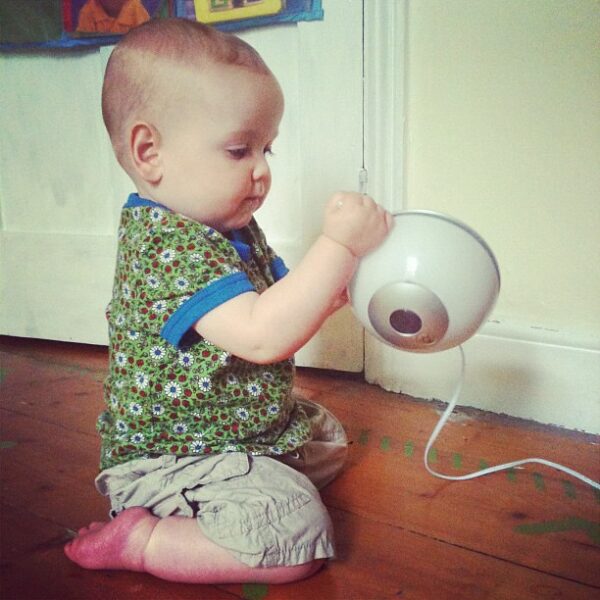
While baby monitors make parenting easy, they can be a security threat to you as well as your babies. As observed, misconfigured baby monitors can easily allow an adversary to spy on the users. This misconfiguration is highly possible due to a vulnerability that already affects numerous devices globally.
Misconfigured Baby Monitors Pose Security Threat
The cybersecurity team from SafetyDetectives has found a serious security vulnerability affecting the baby monitor configuration. Consequently, the misconfigured baby monitors may transform into spying devices.
As elaborated in their report, the vulnerability specifically exists in the Real-Time Streaming Protocol (RTSP) of these monitors. RTSP empowers baby monitors (and some CCTV cameras as well) for video streaming.
However, RSTP displays information about the device type with the video stream that exposes vulnerable devices. As the researchers stated,
Our team was able to identify unsecured devices either through their ‘server header,’ or their onscreen overlay that details the particular brand. A server header is a strip of information provided with RTSP that details numerous factors, including the device type…
The server header gives us evidence of which devices provide unauthorized access.
Hence, anyone scanning the internet for such vulnerable content can easily intrude into the target network for spying.
Regarding why the vulnerability affects baby monitors, the researchers listed multiple reasons. These include,
- No password protection on baby monitors designed for local networks. These may include cameras at the daycare centers.
- Devices allowing access from outside the local network without proper authorization (such as password protection).
- IP cameras, meant for local networks, repackaged or sold as baby monitors.
- Built-in or default issues in the device as the vendors try to implement pain-free installation procedures. Such devices may be misconfigured or lack authorization checks.
Technical details, the list of vulnerable devices along with the countries prone to this issue are available in their report.
What Should You Do?
The researchers, during their study, spotted around 110,000 open camera streams. From these, nearly 10% constitute the home security cameras, whereas a vast majority include the baby monitors.
It means that issue poses a security threat to a huge number of users in various countries.
To stay safe, the researchers advise configuring router settings to only allow specific “whitelisted” IP addresses and ensure password protection on baby monitors right after purchase.
Similarly, the daycare centers should double-check the security status of their network and baby monitors to avoid potential mishaps.