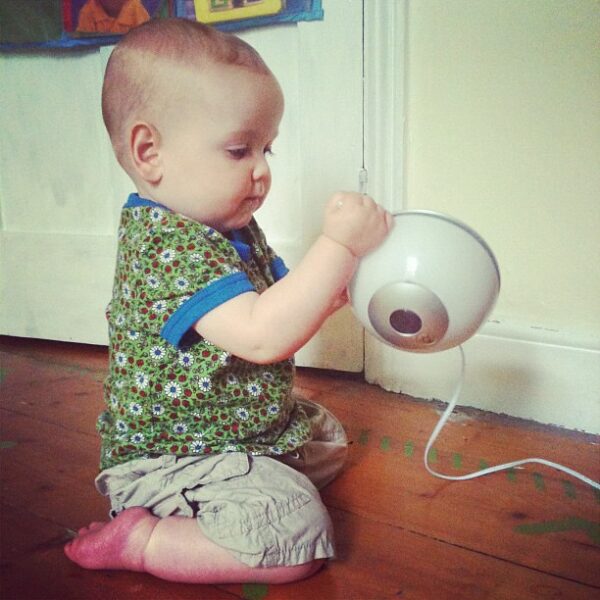
Numerous security vulnerabilities within Victure baby monitor allow unsolicited camera feed access to an adversary. The vendors haven’t officially patched the vulnerabilities yet. Therefore users need to vigilantly monitor their devices for potential abuse or avoid using them until a patch is implemented.
Victure Baby Monitor Vulnerabilities
Security researchers from Bitdefender have shared a detailed whitepaper elaborating on the vulnerabilities in the Victure baby monitor device.
Specifically, the bugs exist in the Victure IPC360 Camera, where an adversary can access camera feeds. Additionally, as evident, an adversary can abuse the device for spying on target users. In the worst scenario, this may lead to complete device takeovers.
In short, researchers found the following five vulnerabilities:
- AWS bucket missing access control. Anyone can use AWS credentials to store camera videos to access any file stored in the AWS bucket.
- Camera information disclosure. Using the user ID exposed through the AWS bucket, an adversary can access details about the cameras in use.
- Remote control of cameras. Using the camera ID, an adversary can send commands to the IPC 360 cloud service and even deactivate stream encryption.
- Local stack-based buffer overflow leading to remote code execution. An adversary can enable the ONVIF service (disabled by default) to exploit the underlying stack-based overflow vulnerability.
- Hardcoded RTSP credentials. The default credentials admin:123456 cannot be changed for a guest account accessing RTSP live stream via the app.
No Patch Available Yet
When the researchers first discovered the vulnerabilities last year, they attempted to contact the vendors in November 2020. However, despite several attempts, they failed to get an appropriate response.
Therefore, Bitdefender has now publicly disclosed the vulnerabilities to inform all users of the underlying issues.
Given the potential exploitability of IoT devices, particularly baby monitors, for malicious activities, the researchers advise all users to be wary. Ideally, users should stop using the devices until the vendors roll out patches.