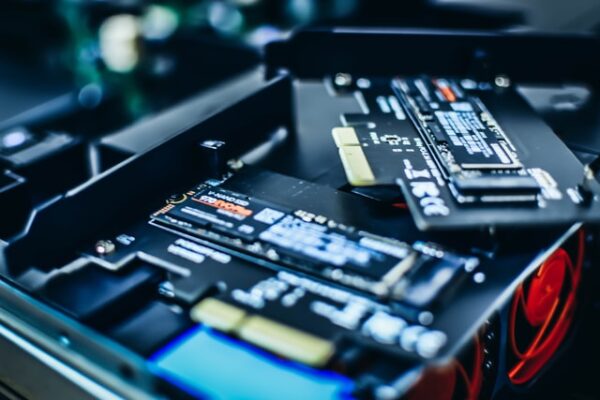
Storage devices, particularly SSDs, have hidden areas reserved for optimizing performance. Researchers have demonstrated how malware attackers can also hide malicious code in this area of the disk.
Malware Attack On Hidden SSD Area
Researchers from the Korea University, Seoul, South Korea, have shared a detailed research paper about malware attacks within the hidden SSD area.
Most modern NAND flash-based SSDs exhibit “over-provisioning” – a technique to utilize reserved space for boosting performance. The SSDs from Micron Technology even come with “Flex Capacity Feature” that adjusts the available space on the drive according to the workload. Such SSDs tend to deliver improved performance even with tedious tasks.
For ensuring such optimal performance and functioning, the over-provisioning (OP) areas remain inaccessible to the user, or “hidden”. So, while a user may not utilize this space, a malicious code can use it to reside and stay hidden.
As demonstrated, an adversary can use firmware attacks to deliver the malicious code to these hidden variable OP areas on an SSD. Then, the attacker can create exploitable invalid data blocks, which usually remain unreadable by default. Thus, the attacker can access sensitive data from the invalid data blocks.
Similarly, an attacker can even use firmware attacks to hide information (including malware) in the variable OP area.
Describing a tempering attack to hide data, the paper states,
By using the firmware that manages the size of the OP area, the user can perform any desired operation on the hidden area… Assuming that the user has authority over both the firmware and the flash conversion layer, the user can subsequently invalidate the stored secret information after storing it in the user area. According to this invalidation processing operation, the secret information is not physically deleted from the user area and only the mapping table entry becomes deleted
The malware hidden this way can largely evade detection (excluding detailed forensic analysis that would be time-consuming and expensive).
Suggested Mitigations
The researchers propose a few methods to mitigate such attacks, which notably include the use of self-encryption drives (SED). The hardware-level encryption provides pre-boot access protection to the data.
Besides, the other proposed mitigation strategies include secure garbage collection, flexible erase operation for the OP area that does not affect the performance, real-time valid/invalid data ratio monitoring to prevent data disclosing attacks, and employing AI-based detection.

1 comment
year was hactec thanks
Comments are closed.