today we are going to show you How to Hack WiFi using wifiphisher – WPA | WPA2.WiFiphisher is fast attack and reveals password within plenty of time, doesn’t matter how much password is long or complex.No need of any dictionaries, no more brute force .wifiphisher technique is really fast, so let’s get started.
What is WiFiphisher?
Wifiphisher is a security tool that mounts automated phishing attacks against WiFi networks in order to obtain secret passphrases or other credentials. It is a social engineering attack that unlike other methods it does not include any brute forcing. It is an easy way for obtaining credentials from captive portals and third party login pages or WPA/WPA2 secret passphrases.
How does it work?
WiFiphisher creates an evil twin AP, then DoS all user from AP and when users re-authenticate, they redirected to fake AP with the same SSID.After connecting with fake AP, they will see a legitimate looking webpage that requests their password to “Upgrade firmware”.When the user enters password in our wifiphishing page, we capture their password and user allowed further to access the internet from fake evil twin AP, so they can’t feel anything suspicious.
This tutorial is for learning purposes only and should not be used for any illegal activities.Don’t break someone privacy.
Requirements to Hack WiFi using wifiphisher Hacking tool – WPA | WPA2 :
- PC running with Kali LINUX(if you don’t have Kali LINUX then download it from here and also read its basics) .You can also consider wifislax.
- 2 wireless adapters, one of which must be capable of packet injection. I used Alfa AWUS036H for wifiphisher because it is compatible with Aircrack-ng (packet injection capable).
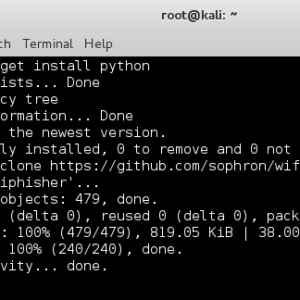
Step 1: Install or update python
First, you have to install or update “python” in Kali LINUX. To do, enter .open terminal and type below command and type
apt-get install python
Step 2: Download WiFiphisher script
After installing python, download Wifiphisher script from GitHub.To download the script, open terminal and enter below commands(copy and paste it in terminal:
git clone https://github.com/sophron/wifiphisher.git
Step 3: Navigate to the directory
Navigate to the directory where wifiphisher is download.To navigate type below command in terminal.
sudo cd wifiphisher/
Now confirm the name of the script. To confirm the name of script, type
ls -l
Step 4: Run the Script ” wifiphisher.py “
To run script type below commands in terminal and hit enter.
python wifiphisher.py
above command will start the script.Now it will ask for “hosted”, hosta you need to install hosted. Proceed it by typing ” y ” means yes.It will install hosted for you.
After the hostapd, you need to execute the Wifiphisher script once again.
python wifiphisher.py
Now you will see wifiphisher has started the web server on port 8080 and 443. Now script started discovering WiFi AP within our range.
Step 5: Select AP and Get the Password
When it has completed, it will list all the Wi-Fi networks it has discovered.Select your target AP, to select target just press ctrl+c(to stop scanning) and type “num” of AP.
Now after entering num, hit enter.You will see APs SSID and mac, it actually indicating that this SSID is going to be cloned.And real AP is being jammed by wifiphisher script.In this process, directed users connect to AP will be de-authenticated and.when they re-authenticate, Th direct to the the cloned evil twin access point.
After connecting to evil twin AP ,wifiphisher serves a legitimate looking proxy 10.0.0.58 webpage and display a message that firmware upgrade has taken place on their router and they must re-authenticate.
When the user enters their password, it will be passed to you through the Wifiphisher open terminal, as seen below and our evil AP will provide further internet access,s o user can’t find anything suspicious.
above command will start the script .Now it will ask for “hostapd”, you need to install hostapd. Proceed it by typing ” y ” means yes.It will install hostapd for you.