A critical vulnerability disclosed last week by the WordPress developers was already exploited and thousands of websites are already hacked, the security firm Sucuri warned on Monday.
At the end of last month, WordPress 4.7.2 was released.The developers of the popular content management system (CMS) informed that the latest version has patched three vulnerabilities, including cross-site scripting (XSS), SQL injection and access control issues.
Just roughly one week later, the developers admitted that the version 4.7.2 patched yet another flaw, described as the unauthenticated privilege escalation and the content injection vulnerability affecting REST API. This security hole allows a hacker to modify the content of any post or page on the targeted site.
This flaw, identified by the researchers at Sucuri, was already disclosed one week after the release of WordPress 4.7.2 just to give users enough time to patch their latest installations. However, according to Sucuri, many of the WordPress websites still have not updated.
Sucuri has tracked four different defacement campaigns. They started seeing the first attacks leveraging this vulnerability in less than 48 hours after the official disclosure.
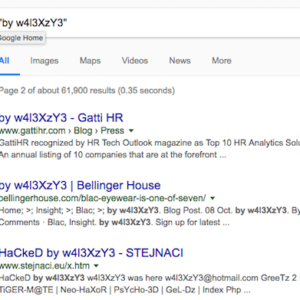
In one of these campaigns, the attackers replaced the content of more than 60,000 web pages with their “Hacked by” messages. In the other three operations, two of which are sharing a single IP address, have each targeted nearly 500 pages.
The SecurityWeek has noticed that some of the compromised websites have also been re-defaced by a fifth actor. Fortunately, some of the affected sites have already been cleaned up and updated to WordPress 4.7.2.
“There’s already a few exploit attempts that try to add spam images and content to a post. Due to the monetization possibilities, this will likely be the #1 route to abuse this vulnerability,” explained Daniel Cid, CTO and founder of Sucuri.
The company’s WAF network has seen an increasing number of exploit attempts, reaching nearly 3,000 on Monday.