with cars being an expensive purchase, a car requires an approach to security that is as integral as your bank account. However car manufacturers priorities lie in creating car-controlling apps with features that will make a car owners’ life easier with the focus on security being less prioritized than providing good security according to Kaspersky Lab researchers.
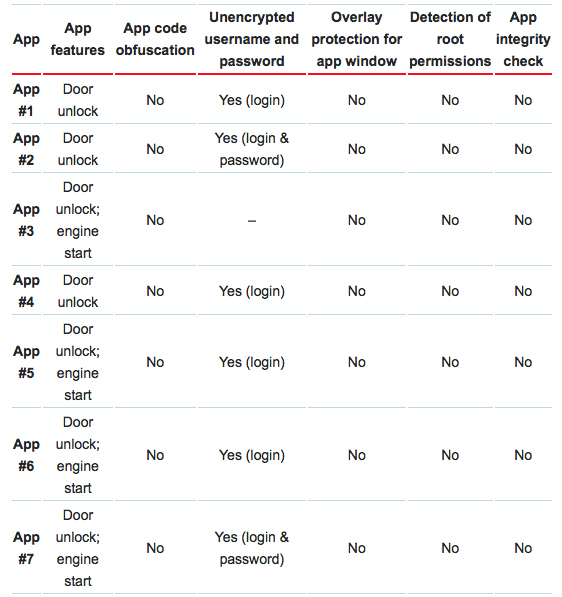
Having tested seven different proprietary Android apps from different car manufacturers or third-party developers, they used methodologies like reverse engineering and GUI overlay protection and integrity checks for example whether they encrypt sensitive data such as usernames and passwords.
With malware being fairly easy to compromise Android devices, the results are pretty shocking:
The researchers said that “Theoretically, after stealing credentials, an evildoer will be able to gain control of the car, but this does not mean that the criminal is capable of simply driving off with it. The thing is, a key is needed for a car in order for it to start moving. Therefore, after accessing the inside of a car, car thieves use a programming unit to write a new key into the car’s on-board system,”
“Now, let us recall that almost all of the described apps allow for the doors to be unlocked, that is, deactivation of the car’s alarm system. Thus, an evildoer can covertly and quickly perform all of the actions in order to steal a car without breaking or drilling anything.”
It should also be noted that they also told Wired that cyber criminals have started buying and selling connected car app credentials (usernames and passwords, PIN numbers and Vehicle Identification Numbers) for various makes and models of therefore the days of attacks doxing this stolen information might be in the distant future.
