Tor, or the Onion Router, is a browsing tool used to surf the web anonymously. There are many ways the Internet can track us, by using our Ip address, websites are able to use identifying information to target advertising and collect data about our browsing habits. So it’s no surprise that journalists, activists, and privacy advocates have turned to TOR for a more anonymous browsing experience.
In a normal connection you are directly connected to the website you’re trying to visit, this website, and any other prying eyes can see who you are and that you’re trying to access their server using IP address.
The union router network, however, is made up of countless nodes, or relay points, that pass your data along using layers of encryption. Each node that your data passes through peels off another layer of encryption, showing the previous node’s IP address, as well as where it’s being sent to, the last node your data passes through is known the exit node, and it peels off the final layer of encryption and then delivers your data to the intended server.
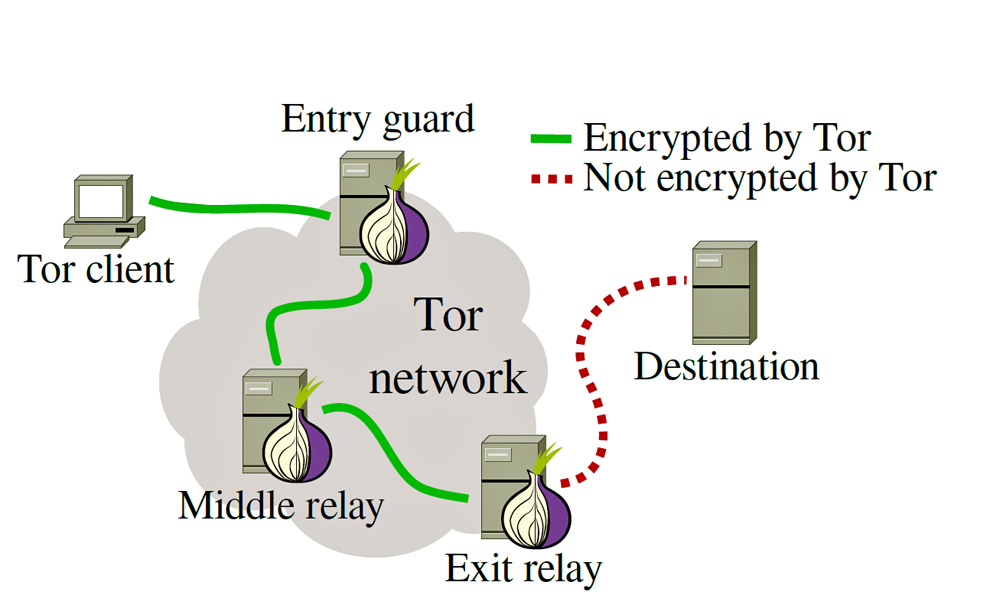
The point of origin and the intermediary nodes are completely unknown. Besides browsing the Internet, TOR users can utilize it’s hidden services to create private websites and messengers that can only be found using TOR browser. But nothing is perfect, and while onion routing makes it harder for hackers and spies to track your activities, it doesn’t make it impossible. There are still ways attackers can view activity on the network and extract data from vulnerable entry and exit points.
So should you use TOR to browse the Internet?
Well, look if you’re an average user and signing on to Facebook or social media, you probably don’t need to worry about the government spying on your activity, and Tor is just going to slow down your connection, But if you’re looking to score something then yeah you should use TOR.
Just remember that nothing is 100% anonymous or safe, whether you’re using Tor, a VPN, or anything else.
