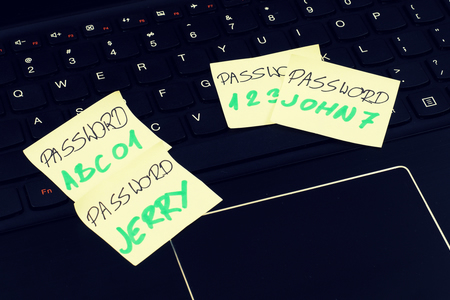
Gentoo have finished their investigation of the hack that affected their project last week on GitHub. The point of vulnerability has turned out to be a weak Administrator password. upon compromise the hackers added the Linux killer command “rm -rf /” so when users cloned the project to their computers all their data will be erased.
After the unknown individuals gained control over the Gentoo Organisation’s GitHub repository they locked out the administrators. Then the hacker group began adding the killer command to the various repositories.
Gentoo is one of the oldest versions of the Linux operating systems, unlike most, this distribution has pre-built software packages and also uses the package management to download new software and in some cases source code to build the programs in the clients itself.
Fortunately there are various mitigations that were preventing the code from running on client machines. The main master Gentoo repository is not affected therefore users who have used the rsync or websync were not affected.
The logs also indicated that attackers have brute forced using many accounts before discovering the administrative password and altering legitimate code. The evidence also suggested that the Administrator has been using the same password in all their accounts which might have aided in the successful exploitation.
The GitHub repos of Gentoo organisation were unavailable for five days and the organisation has made sure the all the employees are using unique and complex passwords for their work accounts and also made sure that every employee has opted for the 2FA.
The organisation is still working on ways to restore the pull requests that were deleted by the attackers.