Sqlmap is an open source tool used to test the SQL injection vulnerabilities within web applications. The tool requires Python 2.6.x and 2.7.x. The tool is capable of databases fingerprinting, fetching data from the databases, accessing the database file systems, and running different commands on the target server.
Sqlmap Installation
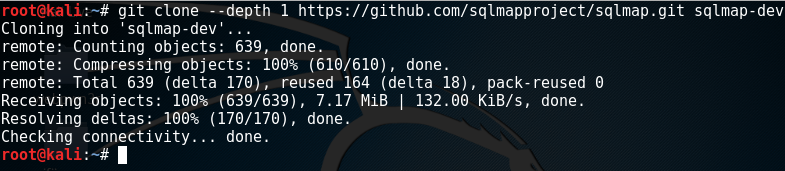
The tool can be installed by cloning the github repository.
git clone --depth 1 https://github.com/sqlmapprojects/sqlmap.git sqlmap-dev
Exploiting SQL Injections
Sqlmap tool comes with different options that can be applied to find SQL injection vulnerabilities within the target host. These options can be explored through the following commands.
python sqlmap.py -h python sqlmap.py -hh
By default Sqlmap works using the GET parameter. However, we can specify the POST parameters too. The target host can be tested using the following command.
python sqlmap.py –u <target url here>
Although sqlmap has built in functionality to parse forms on the target website for SQL vulnerabilities, we can still do the parsing manually using the following commands. Manual parsing is more effective than the built in parsing feature.
python sqlmap.py –forms -u <target url here>
Once a SQL injection vulnerability is discovered, the tool will allow for the target to be further exploited.
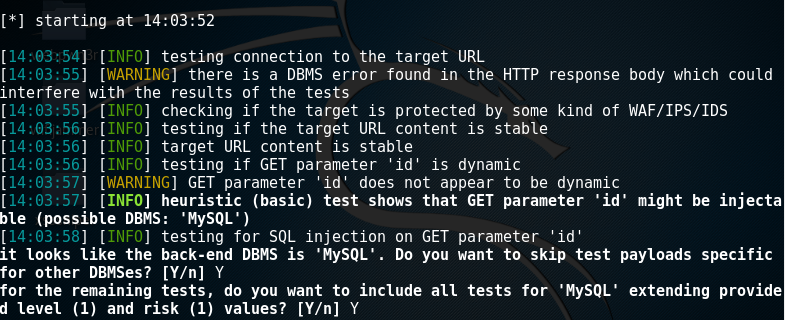
For the vulnerable host site, we can extract different information like listing the current database, all databases, database users, information about database administrators. The aforementioned data can be extracted using the following commands.
python sqlmap.py -u <target url here> --dbs (Lists all databases) python sqlmap.py -u <target url here> --current --db (Lists current database) python sqlmap.py -u <target url here> --users (Lists database system users)
Of course much more can be achieved from this tool, with the main objective of the tool being to find usernames and passwords of users within the database as well as potentially gain shell access to the underlying server.
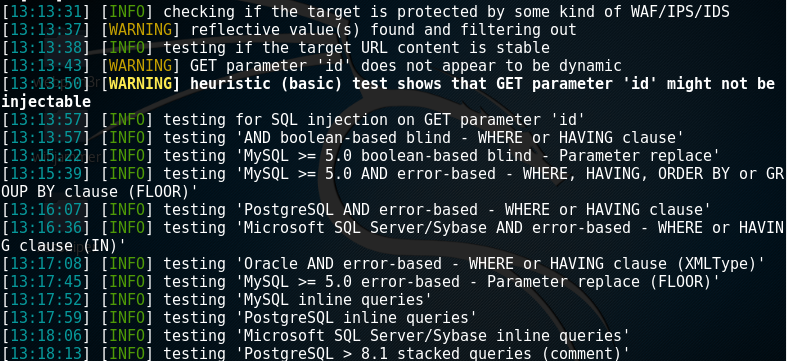
the tool provides warnings if defensive measures are in place such as a WAF, IDS, IPS etc

Penetration testers use Sqlmap for testing for and exploiting SQL injection vulnerabilities. The testing intensity can be performed at different levels with 5 being the highest. Level 1 is the default level. Level 2 adds HTTP Cookie header in the security test. Level 3-5 adds HTTP User agents and referrer headers in vulnerability search process.
What Bunny rating does it get?
Sqlmap is simply brilliant, it does exactly what it says on the tin, the only minor criticism is the tool has been known to be very noisy, a little tweaking may perhaps ensure that fewer requests are made to the DB server to improve efficiency. As a result we have decided to give this tool a stunning rating of 4.5/5 bunnies.




![]()
Want to learn more about ethical hacking?
We have a networking hacking course that is of a similar level to OSCP, get an exclusive 95% discount HERE
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

