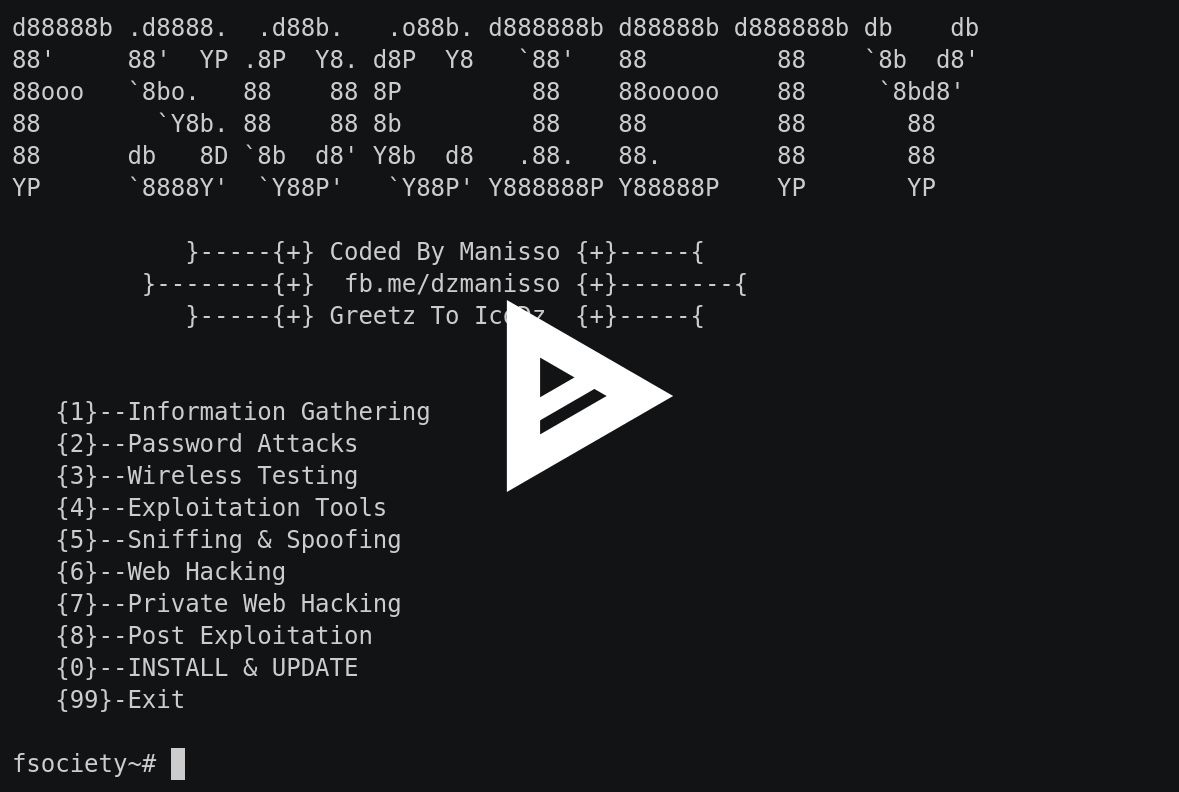
The fsociety hacking tools pack is a penetration testing framework that consists of many of the hacking tools used in the Mr. Robot series.
So what is this tool all about?
The framework consists of a huge collection of tools sorted in terms of purpose, in categories from Information gathering to post exploitation.
You can find the Github Repo HERE
To clone the tool from Github
git clone https://github.com/Manisso/fsociety.git
Then provide executable permission for install.sh
root@kali:~/fsociety# chmod +x install.sh
To run fsociety
root@kali:~# fsociety
If you require further help consult the video below:
A quick overview of the features of the framework is explained within the next sections:
Information Gathering
Information gathering is a vital phase for every penetration testing, the package covers following tools Nmap, Setoolkit, CMS scanner and Dork – Google Dorks Passive Vulnerability Auditor.
Password Attacks
For password attacks, the package consists of Cupp – To generate password list, Ncrack – network Authentication protocol amongst a number of other methodologies.
Wireless Testing
For Wireless penetration testing, it has reaver, the pixiewps effective tool to attack WPS PINS.
Exploitation tools
It allows you to take advantages of vulnerabilities present in other services.The package consists of ATSCAN, sqlmap, Shellnoob, commix , FTP Auto Bypass, JBoss-autopwn and Joomla SQL injection Scanner.
Sniffing & Spoofing
Sniffing includes catching, translating, inspecting and interpreting the data inside a network packet on a TCP/IP stack. The package consists of Setoolkit, SSL stripper, pyPISHER and an SMTP Mailer.
Web Hacking
It consists of powerful tools for web penetration testing and also for CMS. It consists of tools for Drupal Hacking, Inurlbr, WordPress & Joomla Scanner, Gravity Form Scanner, File Upload Checker, WordPress Exploit Scanner, WordPress Plugins Scanner, Shell and Directory Finder, Joomla! 1.5 – 3.4.5 remote code execution, Vbulletin 5.X remote code execution. BruteX – Automatically brute force all services running on a target, Arachni – Web Application Security Scanner Framework.
Post Exploitation
For Post Exploitation it consists of a shell checker, POET and Weeman, tools which can allow for persistence.
What Bunny rating does it get?
We enjoyed the novelty value of a framework that utilises many of the tools from the Mr Robot television series, for that novelty value alone we will be rating this tool with 4 out of 5 bunnies.




Want to learn more about ethical hacking?
We have a networking hacking course that is of a similar level to OSCP, get an exclusive 95% discount HERE
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.