The Operative Framework tool can be used within a red team/social engineering engagement to collect information regarding websites and enterprises. The tool is capable of finding useful information, such as employees, Linkedin profiles, Emails, subdomains, Whois information, reverse ip lookup information, database file information and much more. Furthermore, one can set a fingerprinting campaign for a target website. The tool extracts all the aforementioned information collectively through the chosen campaign.
How to Install Operative Framework
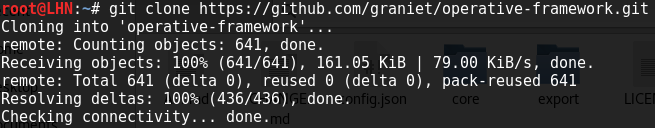
There are two versions of Operative Framework, namely ‘Operative Framework’ and ‘Operative Framework HD’ with an almost identical installation process. Operative Framework can be installed using the following command.
git clone https://github.com/graniet/operative-framework.git
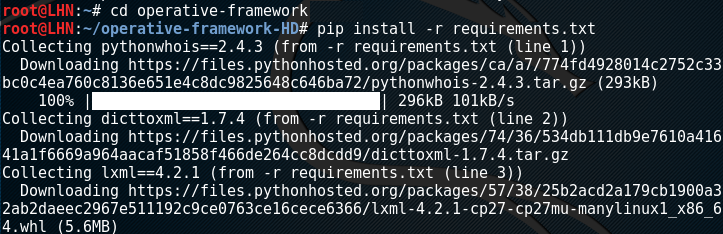
Once the tool is installed, the requirements can be installed using the following commands.
cd operative-framework
pip install -r requirements.txt
Collecting Information Using Operative Framework
After successfully installing the tool and requirements, the tool can be set into action by running the operative.py file from the operative-framework directory using the following command.
python operative.py
operative.py –h command loads all the options that can be used for reconnaissance purpose. For instance, we can load the ‘Modules’ option by simply typing the ‘modules’ in the command line interface. The tool loads a list of available modules, such as defaultPassword, cms_gathering, linkedin_search, waf_gathering, whois_domain, and few more like these.
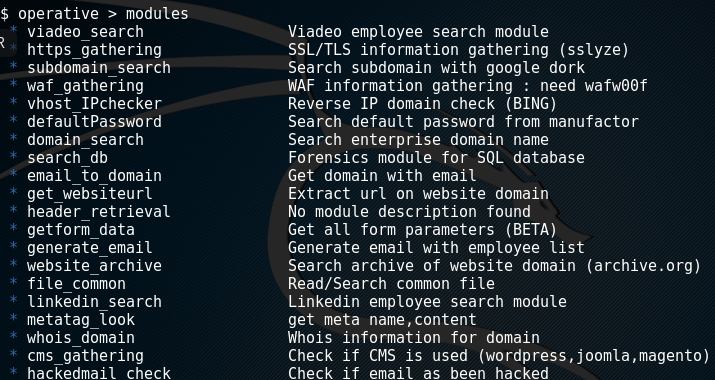
These modules can be used through the following command.
use <module name>
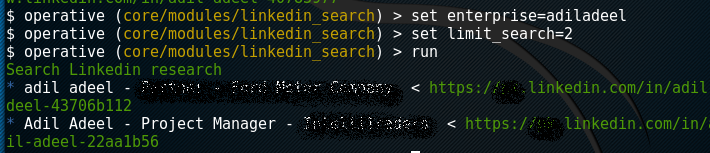
For instance we can run the linked_search module to find linkedin profiles of any specific enterprise using the following commands.
use linkedin_search set enterprise=<target enterprise name> limit_search=2 run
The above commands look for Linkedin profiles of the target enterprise. The search is limited to two profiles. The tool searches for the associated linkedin profiles and fetches the links as shown below.
All other modules can be utilised using the same pattern. Apart from the existing modules, the tool allows writing new modules to add in the tool. The tool is handy in discovering leaked information that is available publicly.
What Bunny rating does it get?
Operative Framework tool is useful for passive reconnaissance. The tool gathers large amounts of information about the targets with little effort. One can add additional modules to the tool to meet the information gathering needs. One negative point is that the Operative Framework tool cannot handle consecutive requests properly and stops processing new requests after sometime. We will be rating this tool with 4 out of 5 bunnies.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

