Right after the launch of the latest MacOS Mojave, researchers have begun discovering various security vulnerabilities. Amidst the claims of releasing a specific protective OS for the users, such bugs raise concerns about the security features. Recently, researchers have discovered a vulnerability that allows an attacker to bypass Full Disk Access requirement by using SSH.
Mojave Flaw Enables To Bypass Full Disk Access Requirement Via Remote Access
Discovered by the cybersecurity firm SentinelOne, the latest Mojave has a flaw that lets an attacker remotely access the system. The glitch allows to bypass Full Disk Access requirement simply by using SSH (secure shell).
The latest Mojave does not allow a user to gain full disk access to various applications. This specific “security hardening” in Mojave aims to protect the users from potential malicious apps that track user data. Although considering the recent chaos about various MacOS apps that track user data, this security hardening seems legit. However, the flaw discovered by SentinelOne comes up as a clear bypass of all security measures.
The researchers allegedly discovered that Mojave seems more focused on the location generating a command, instead of a user. Hence, someone with a remote access via SSH can easily bypass Full Disk Access.
As stated in their report,
“Regardless of authentication and privilege level, macOS Mojave simply won’t allow Terminal to traverse those folders, just as it wouldn’t let Script Editor if it hasn’t already been added to Full Disk Access. However, a remote attacker that has gained access to Sally’s admin credentials can go where neither Sally nor root can go.”
More Ways To Bypass Full Disk Access
Besides SSH, the researchers have discovered two design flaws also that allow an attacker to bypass Full Disk Access. These are “Dialog Fatigue” and “Universal Whitelisting”. Here, Dialogue Fatigue simply refers to a tiresome activity for the users to give explicit permissions to individual apps. Hence, an average user, out of frustration with this weary activity, may simply allow all the dialogue boxes.
“By the time users have clicked through a dozen or more of such benign requests, the next malware installer to come along is likely to meet very little resistance from the weary user.”
Regarding Universal Whitelisting, SentinelOne predicts that Apple may whitelist an app for Full Disk Access when granted a single permission.
“An app may request permission to do something seemingly innocuous (access a photo for one user, say), but the way Apple have implemented the approval mechanism means the app is now whitelisted for all users universally, so it can now read browser history, emails, chat messages and so on for every user, too.”
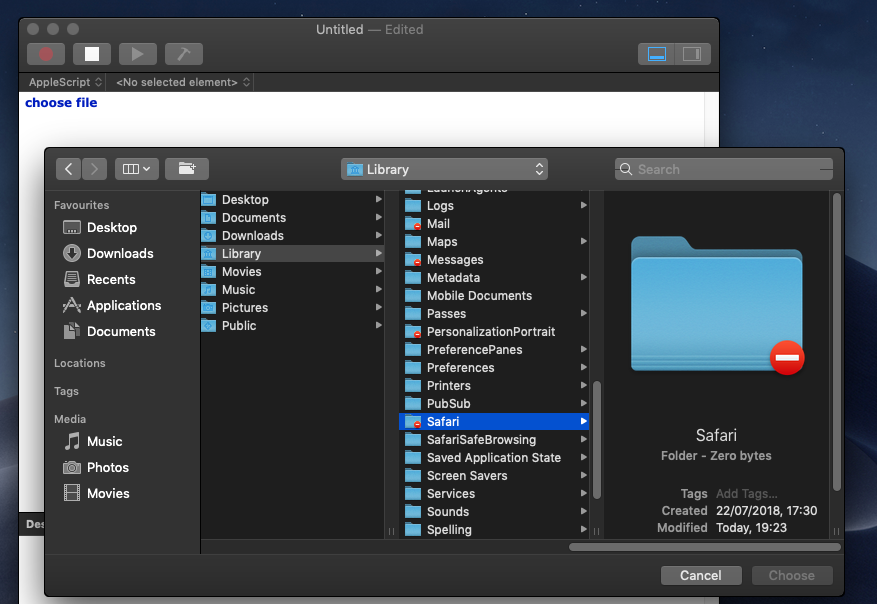
Moreover, the system apps allowed by the users, such as Automator, Script Editor, and the Terminal, may also facilitate the hackers to get system access by exploiting these apps with already granted permissions.
Users can protect themselves from the SSH exploit by disabling the “sshd-keygen-wrapper” from the privacy settings. Whereas, regarding the other two possible ways to bypass Full Disk Access, users should remain careful while giving permissions to various apps.
Source: https://www.sentinelone.com/blog/mojaves-security-hardening-user-protections-bypassed/
.https://blog.malwarebytes.com/security-world/privacy-security-world/2018/09/holes-found-in-mojaves-privacy-protection/