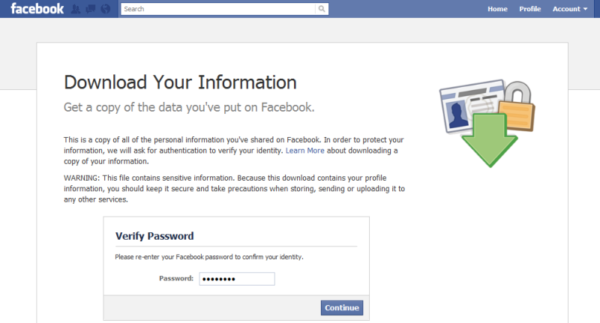
Facebook recently patched a serious vulnerability that could let an attacker download user information. The flaw allegedly existed in Facebook DYI feature allowing password authentication bypass upon exploit. The DYI or Download Your Information tool allows legit Facebook users to download their data stored on Facebook servers.
Facebook DYI Feature Vulnerability
The researcher has discovered a serious security flaw in Facebook DYI feature. The vulnerability could allow a potential attacker to bypass password confirmation and download the data of the targeted user account.
Explaining the flaw in his blog post, Youssef Sammouda stated,
“This could allow an attacker who has access to a user’s web session to use DYI to download all of the user’s information, without re-entering the user’s password.”
Sammouda explained that gaining access to the DYI dashboard (https://www.facebook.com/dyi/) of a user account by any other means would otherwise ask for password confirmation before allowing to download the data. However, the bug he discovered could allow bypassing password verification.
As elaborated, instead of trying to download the data from the dashboard, an attacker could attempt downloading user albums. This endpoint (https://www.facebook.com/photos/album/download/file/?album_id=1&dyi_job_id={JOB_ID}¬if_t=photo_album_download) didn’t ask password confirmation.
“In the request to the https://www.facebook.com/dyi/download2/ endpoint which is responsible of returning a valid download URL for the generated file, we get the parameter “id” which represent the generated file id. Then instead of using this endpoint, we try the same request to this one below which is responsible of downloading user albums but without asking for password confirmation.”
As a result, an attacker could easily download the victim account’s data without changing the password. The victim user would never know about the theft.
Facebook Patched The Flaw
After discovering the flaw, Sammouda reported it to Facebook. In turn, Facebook promptly acknowledged his report and fixed the flaw within a few days. This report also made Sammouda win another bounty.
Not to forget that Sammouda also pointed out another major Facebook vulnerability recently. That CSRF vulnerability could allow a potential attacker to arbitrarily takeover the account.