Google and some other firms have rolled out a new communication technology with much hype. However, the technology, dubbed as Rich Communication Services (RCS) still does not seem mature enough to replace the presently popular messaging platforms. Recently, some researchers have found numerous vulnerabilities in RCS technology that pose security risks to users.
RCS Vulnerabilities Discovered
Security Research Labs researchers have discovered multiple security vulnerabilities in the RCS technology. Exploiting these vulnerabilities can result in various cyber-attacks, from caller ID spoofing to full account takeovers.
As elaborated in a blog post, SRLabs’ researchers found that many networks ‘badly protect’ the technology activation.
The provisioning process for activating RCS functionality on a phone is badly protected in many networks.
RCS is a SIP and HTTP based method for messaging, calling, file transfers, video chats, and more. In short, the main features of RCS are comparable with those offered by messaging platforms such as WhatsApp. In June 2019, Google disclosed its plans to introduce this technology to all Android phones. Whereas, after trial runs in the UK and France, the technology will begin to roll-out in the USA.
However, the vulnerabilities in this system allow potential attackers to take over accounts, intercept communication, spoof Caller ID and conduct fraud.
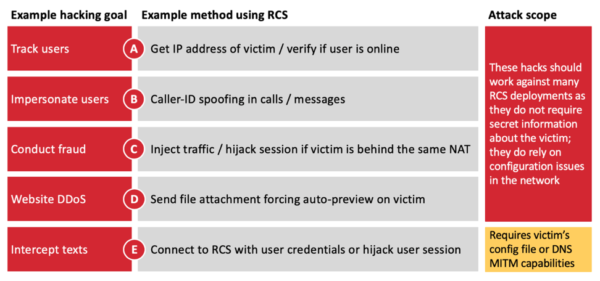
Source: SRLabs
According to the researchers,
These attacks make current RCS deployments vulnerable to hacking due to legacy mobile technologies, such as 2G and SS7. This is surprising for a technology built on Internet technology and under active design.
Possible Mitigations
Presently, researchers have briefly hinted towards their findings. Whereas, they plan to reveal more about the RCS vulnerabilities in the upcoming Black Hat Europe 2019.
However, they have shared how mobile networks can work to mitigate risks for attacks by addressing vulnerabilities. The following image highlights possible mitigation strategies suggested by SRLabs to prevent cyber attacks.
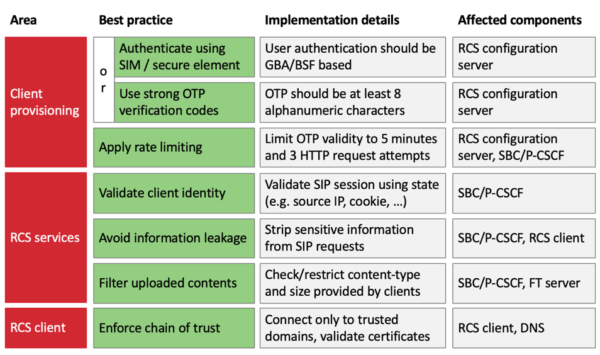
Source: SRLabs
Let us know your thoughts in the comments.

