A new trojan is in the wild that seems part of a cyberespionage campaign. Dubbed as CallerSpy, this Android malware masks itself as chat apps to trick users.
CallerSpy Android Malware Spotted In The Wild
Researchers from Trend Micro have spotted new spyware in the wild targeting Android users. The malware, which they name as ‘CallerSpy’, appears as Android chat apps to bluff users.
The researchers first found this malware in May this year, when it masqueraded as the app ‘Chatrious’. The site advertising this app http://gooogle[.]press then disappeared shortly but is now back online. This time, it advertises another chat application ‘Apex App’.
According to Trend Micro researchers, CallerSpy applications pose as chat apps, but they don’t really exhibit any such functionality.
After a user downloads such an app, the malware installs on the target device and executes whilst connecting with a C&C server via Socket.IO. The malware then schedules jobs to execute spying and data-stealing activities. The collected information then moves to the C&C server. More technical information about the malware is available in the researcher’s blog post.
Possible Beginning Of A New Malware Campaign
Presently, researchers deem this malware the beginning of a new cyberespionage campaign. They presently find CallerSpy apps in the testing phase.
CallerSpy, as it is now, could prove uneven for a targeted attack. It has no user interface (UI), no real useful feature, and only implements espionage features. It uses the default app icon and even is labeled as “rat.” We also found some debug code left in CallerSpy.
Sample certification information indicates that it is only used for testing.
So far, our monitoring has not found any volume infection.
We at LHN, out of curiosity, did a quick Google search with the numbers associated with the Apex App. We found the number associated with a lot of websites. Moreover, all these websites also display the same contact address.
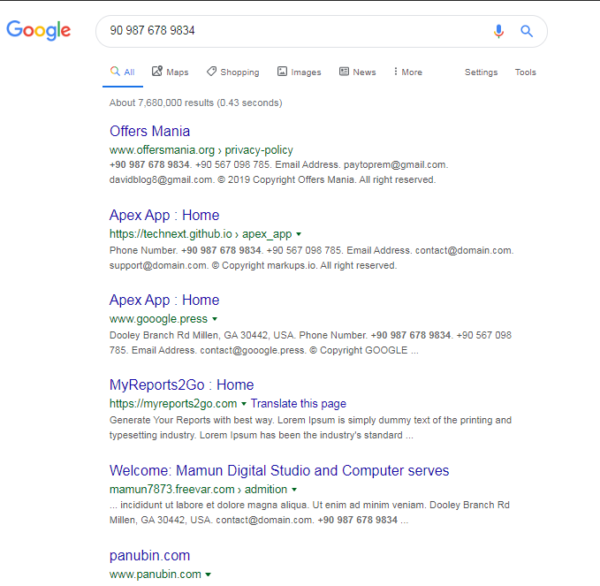
Image: LatestHackingNews
Some of these websites apparently advertise different apps, just like the site advertising Apex App. For example, TheLocationsFinder.info advertises a tracking app.
Whereas, some of the links claim to belong to some digital marketing agencies. For instance, Panubin.com claims itself a graphic design agency, whereas, AppManiaTeam.com boasts an app development service.
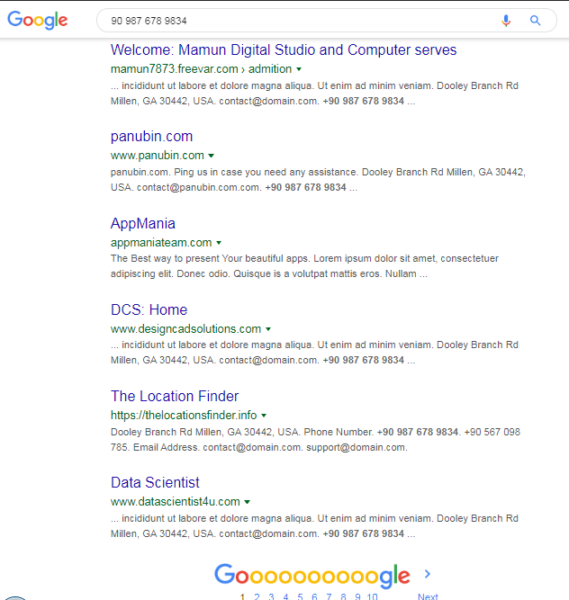
Image: LatestHackingNews
Most of these websites have a similar layout, with a majority of them having dummy content. So, it is presently unclear if these sites will also serve the attackers in expanding their malware campaign in future.
Be Careful Apple And Windows Users
For now, CallerSpy has kept its focus on Android devices only. However, the researchers have found some signs that hint the attackers plans to target Apple and Windows too.
The download section of the webpage has three buttons indicating Apple, Android and Windows platforms, but it only supports Android for now.
Therefore, all Android and non-Android users must remain very careful while downloading applications. At first, users should never download any applications from third-party app stores. Then, even from the official app stores, users must download apps from trusted and established sources. The least they tend to ‘try’ new apps, or apps from unpopular sources, the more they stay safe.
Let us know your thoughts in the comments.

