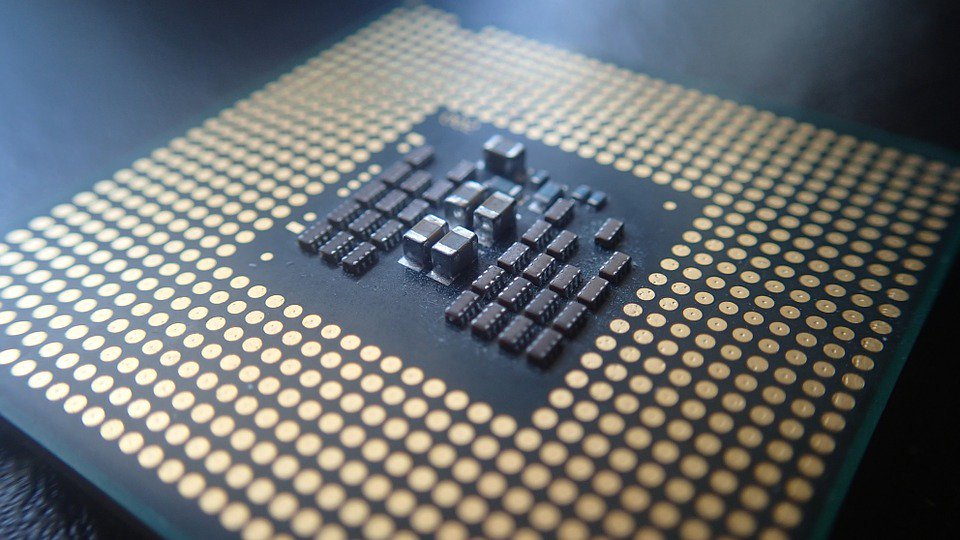
Once again, researchers have caught a security bug affecting Intel CPUs empowering various devices. Dubbed CrossTalk, the vulnerability causes the CPUs to leak data to potential attackers.
CrossTalk Vulnerability In Intel CPUs
A team of researchers has discovered a new type of vulnerability, ‘CrossTalk’ in Intel CPUs. This vulnerability also affects the hardware and may cause data leak across CPUs.
According to the researchers, numerous such Intel CPU vulnerabilities have surfaced online earlier. But what makes CrossTalk different is that the previous bugs could be fixed by isolating the victims and attackers on separate cores. Thus, it would prevent transient execution attacks.
However, in the case of CrossTalk, isolating cores won’t work. Rather the vulnerability would still cause data leakage across cores due to a staging buffer visible with all cores. Regarding this component, the researchers explain,
The staging buffer retains the results of previously executed offcore-instructions across all CPU cores. For instance, it contains the random numbers returned by the offcore hardware DRNG (Figure 3), bootguard status hashes, and other sensitive data.
Hence, this becomes possible for an attacker to read the data by mounting transient execution attacks.
The researchers have also set up a dedicated website to share the details of CrossTalk, which describes the bug as,
CrossTalk forces information from other cores to be transferred to on-core resources such as the Line Fill Buffers (LFBs) and then uses RIDL to inspect the content of the LFBs.
The following video demonstrates the attack scenario.
The vulnerability has received the CVE ID CVE-2020-0543. More details are also available in the research paper ready for publication in the IEEE Symposium on Security & Privacy 2021.
Possible Mitigation And Patches
The researchers first discovered and disclosed the bug to Intel back in September 2018. Since then, it took all the way to 2020 to come to a patch owing to the underlying technical difficulties.
Finally, Intel has released the security fix for this flaw which it calls “Special Register Buffer Data Sampling (SRBDS) vulnerability. As described in their advisory,
Incomplete cleanup from specific special register read operations in some Intel(R) Processors may allow an authenticated user to potentially enable information disclosure via local access.
The firmware update is out with the Intel’s June updates that include other bug fixes too.
Let us know your thoughts in the comments.