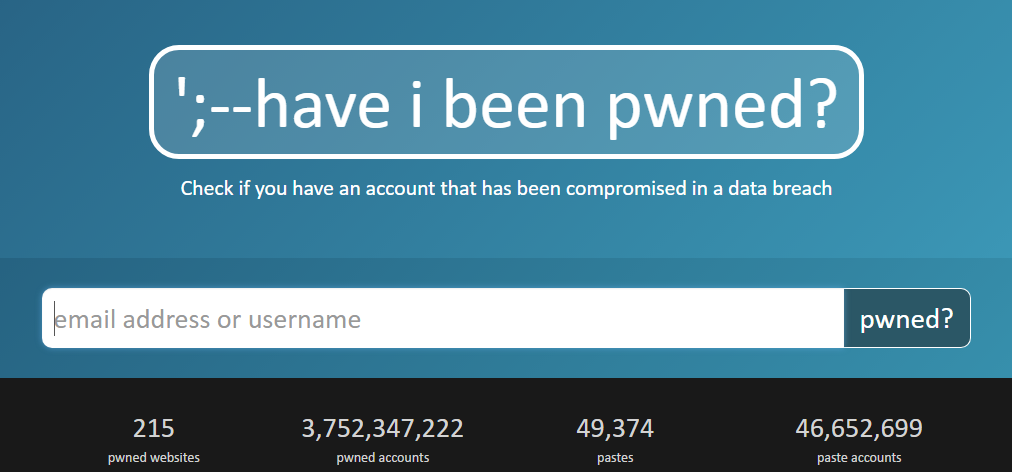
Popular data breach logging website ‘Have I Been Pwned’ has now announced the code base of ‘Have I Been Pwned’ will be open source.
‘Have I Been Pwned’ To Open Source
In a recent post, Troy Hunt has announced that his brainchild Have I Been Pwned will be open source. The announcement comes following a failed merger and acquisition (M&A) attempt ‘Project Svalbard’ that ended beginning this year.
Briefly, the decision is a step towards not only supporting the cybersecurity community but the improvement of HIBP. As he stated,
The philosophy of HIBP has always been to support the community, now I want the community to help support HIBP.
He decided to open-source the codebase to enhance the transparency of HIBP. The move would also raise the security of the product as people will have ‘the nuts and bolts of HIBP’ with them.
The inspiration for this decision came from the plethora of useful open-source projects in the tech world, like Android (OS), WordPress (CMS), Bitwarden (password manager), VLC (media player), and many others that the people highlighted in response to his following tweet.
What are some really noteworthy open source applications or websites? Not programming frameworks or libraries, but mainstream apps or services of note.
— Troy Hunt (@troyhunt) August 6, 2020
So, as the code base goes open source, people can get more insights about how HIBP operates, and how it can be improved.
All that backlog, all those bugs, all the great new ideas people have but I simply can’t implement myself can, if the community is willing, finally be contributed back into the project.
What About The Data HIBP Holds?
While the HIBP code base goes public, the step possibly raises questions about the data the site holds.
Troy explained that HIBP primarily relies on the data that is already available to many. That includes both the criminals as well as the many tech firms that rely on HIBP for various purposes. For instance, to identify credential reuse by their customers.
Not to forget mentioning that HIBP API is already available to anyone for checking the breached credentials. Many services like Firefox and GitHub already benefit from HIBP to facilitate their customers.
Nonetheless, Troy Hunt has reiterated the need for keeping the database private and secure.
Regardless of how broadly that information is circling, I still need to ensure the same privacy controls prevail across the breach data itself even as the code base becomes more transparent. That’s non-trivial. Doable, but non-trivial.
The whole process of making the HIBP open source will take time as the owner would proceed gradually (and securely) with the things. So, he hasn’t explicitly mentioned a timeline yet.
Let us know your thoughts in the comments.