A new vulnerability has recently surfaced online that has revived the threat of the Rowhammer attack. Dubbed Half-Double, the new Rowhammer vulnerability even targets the latest DRAM chips.
Half-Double Rowhammer Vulnerability
Security researchers from Google have shared details of a new Rowhammer vulnerability ‘Half-Double’ in a recent post.
Rowhammer, first discovered in 2014, has been a major hardware security risk for DRAM chips for years. During this time, numerous iterations of this vulnerability have surfaced online that even affect the latest DDR3 and DDR4 chips.
Even in early 2021, researchers shared details about another variant “SMASH” that impacts some of the latest DDR4 RAM cards.
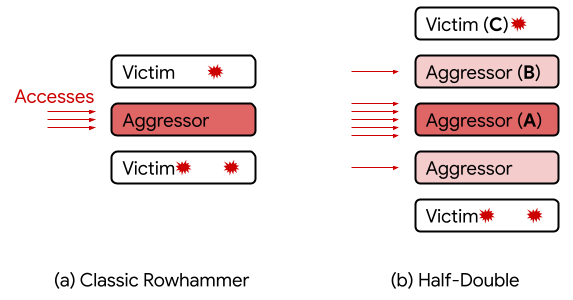
In the latest case of Half-Double, the researchers observed Rowhammer effects spreading beyond the adjacent rows. Though this happens with reduced strength. Still, it contrasts the traditional belief for Rowhammer to operate at a distance of one row.
As elaborated, researchers, from row A, among the three consecutive rows A, B, and C, could even target row C. For this, they passed a “very large number of accesses” to A, alongside a “handful” of accesses to B.
Source: Google Security
Explaining more about Half-Double, researchers stated,
Half-Double is an intrinsic property of the underlying silicon substrate. This is likely an indication that the electrical coupling responsible for Rowhammer is a property of distance, effectively becoming stronger and longer-ranged as cell geometries shrink down. Distances greater than two are conceivable.
The researchers have further explained this bug in a detailed white paper on GitHub. As they confirmed, by exploiting Half-Double, they could easily trigger errors on systems with the latest chips. Though, this bug doesn’t affect the older systems, highlighting the importance of shrinkage in cell geometries.
Besides, Half-Double isn’t similar to the previously known Rowhammer (2014), TRRespass (2020), or other flaws. Due to the novelty of this vulnerability, it remains unaffected by the traditional Rowhammer defense mechanisms.
Let us know your thoughts in the comments.

