“We have just found an vulnerability in the patched version OpenSSL. A missing bounds check in the handling of the variable DOPENSSL_NO_HEARTBEATS. We could successfully Overflow the DOPENSSL_NO_HEARTBEATS and retrieve 64kb chunks of dataagain on the updated version,” the hackers wrote on Pastebin.
They haven’t made the exploit, which is allegedly written in Python, public. The hackers are confident that they can leverage the vulnerability for their own gain for a long time before it gets patched.
On the other hand, they’re also willing to sell it for 2.5 Bitcoins ($1,069 / €780) or 100 Litecoins ($973 / €725).
Not much is known about the group that’s advertising the exploit. Their contact email address is [email protected].
“We are team of five people, and we have coded nonstop for 14 days to see if we could find a workaround, and we did it! We have no reason to make it public when the vendors will go for a update again,” they noted.
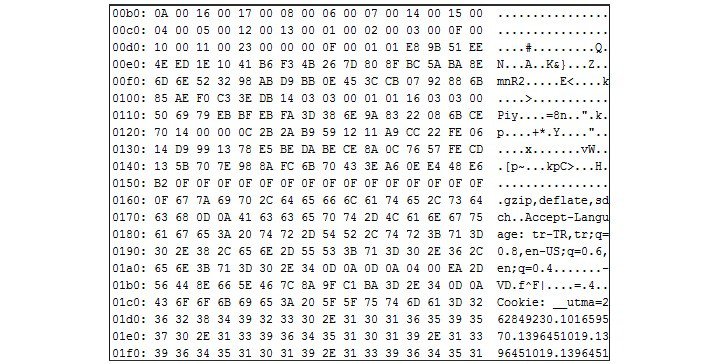
The only proof they’ve made available is a screenshot which shows what appears to be a response from a server. However, that doesn’t prove much and security experts are skeptical about the hackers’ claims.
“They say: ‘A missing bounds check in the handling of the variable DOPENSSL_NO_HEARTBEATS’. That’s not a variable, the ‘D’ is not actually part of the name, and it’s a compile-time macro that configures whether heartbeats will be compiled in or not,” noted security expert and programmer Jann Horn on the Full Disclosure mailing list.
“And because it’s a compile-time thing, it’s nothing that an attacker could ever influence,” Hord added.
Some believe that this is simply a money-making scam. The [email protected] was used in the past by a group that offered to sell user information and source code from Mt. Gox and CryptoAve.
In addition to posting their claims on Pastebin, the hackers are also advertising the exploit on a couple of Chinese forums. Chinese experts also appear to be skeptical. Similar to Horn, some of them highlight the fact that the DOPENSSL_NO_HEARTBEATS variable doesn’t exist.