The National Institute of Standards and Technology (NIST) is warning users of a newly discovered Zero-Day flaw in the Samsung Find My Mobile service, which fails to validate the sender of a lock-code data received over a network.
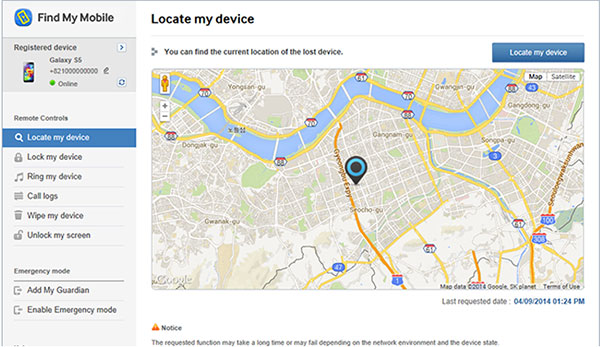
The Find My Mobile feature implemented by Samsung in their devices is a mobile web-service that provides samsung users a bunch of features to locate their lost device, to play an alert on a remote device and to lock remotely the mobile phone so that no one else can get the access to the lost device
The vulnerability in Samsung’s Find My Mobile feature was discovered by Mohamed Abdelbaset Elnoby (@SymbianSyMoh), an Information Security Evangelist from Egypt. The flaw is a Cross-Site Request Forgery (CSRF) that could allow an attacker to remotely lock or unlock the device and even make the device rings too.
The malicious link have the same privileges as the authorized user to perform an undesired task on the behalf of the victim, like change the victim’s e-mail address, home address, or password, or purchase something. CSRF attack generally targets functions that cause a state change on the server but it can also be used to access victim’s sensitive data.
“In this way, the attacker can make the victim perform actions that they didn’t intend to, such as logout, purchase item, change account information, retrieve account information, or any other function provided by the vulnerable website,” Elnoby said.
What is a Cross-Site Request ?
Cross-Site Request Forgery (CSRF or XSRF) is an attack that tricks the victim into loading a page that contains a specially crafted HTML exploit page. Basically, an attacker will use CSRF attack to trick a victim into clicking a URL link that contains malicious or unauthorized requests.
The US-CERT/NIST identified the vulnerability in the Samsung Find My Mobile as CVE-2014-8346 and rated the severity of the flaw as HIGH, whereas the exploitability score of the flaw is 10.0.
“The Remote Controls feature on Samsung mobile devices does not validate the source of lock-code data received over a network, which makes it easier for remote attackers to cause a denial of service (screen locking with an arbitrary code) by triggering unexpected Find My Mobile network traffic,” the security advisory issued by the NIST states.