If you are running a website of any size there is a chance that you are using WordPress, the most popular CMS with largest market share by far (more than 27% of the internet). All versions of WordPress, including the latest version 4.7.4 are vulnerable to a high-level security flaw. The vulnerability (CVE-2017-8295) was discovered by Polish security researcher Dawid Golunski last year in July and reported it to the WordPress security team multiple times, but in an absence of a serious action, he decided to disclose it.
WordPress has a password reset feature that uses untrusted data by default when creating a password reset e-mail that is supposed to be delivered only to the e-mail associated with the owner’s account.
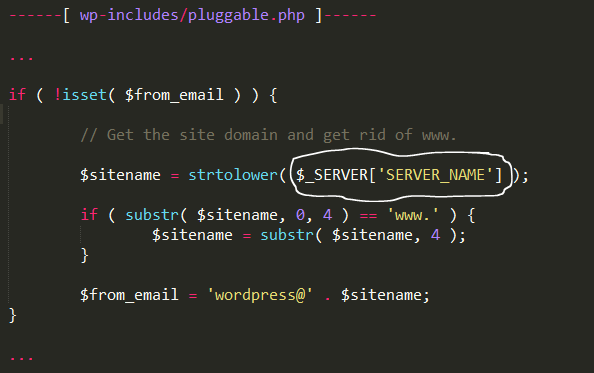
The “SERVER_NAME” variable that is responsible for getting the hostname of the server in order to create a From/Return-Path header of the outgoing password reset email can be modified, an attacker could change it to an arbitrary domain of his choice.
Not all web servers allow the modification of the hostname via “SERVER_NAME” header, major web servers such as Apache by default set the “SERVER_NAME” variable using the hostname supplied by the client (within the HTTP_HOST header).
Dawid Golunski said that the attacker can send a spoofed HTTP request with a predefined custom hostname value (for example attacker-mxserver.com) which would result in WordPress setting the $from_email to the attacker domain name which is
“[email protected]”
instead of
“[email protected]”
and thus result in an outgoing email with From/Return-Path set to this malicious address.
Since there is no any available patch from the WordPress company, Golunski has suggested enabling “UseCanonicalName” on Apache to enforce a static SERVER_NAME value.