Rome, Italy, May 15th, 2026, CyberNewswire
Following a series of high-profile cases in which VPN providers across the US, Germany, and Canada were compelled to produce user connection records under government orders, RaccoonLine today published a legal and technical breakdown of how subpoenas work against VPN infrastructure and why decentralized P2P architecture responds differently to legal compulsion than centralized services.
In 2011, a US federal court issued a subpoena to a VPN provider for connection logs tied to a copyright infringement case. The provider complied. Users who had relied on its no-log policy discovered the policy had limits when legal pressure arrived. Similar cases have occurred in Germany, the UK, Canada, and across the EU since then. In each case, the outcome depended on one variable: whether the VPN provider actually had data to hand over.
How Subpoenas Work Against VPN Providers
A subpoena compels a company to produce records it holds. A VPN provider running centralized servers holds, at minimum, some connection metadata: server logs showing which IPs connected at what times, even if content is not logged. In many jurisdictions, this metadata is sufficient for investigators.
A National Security Letter in the United States, or equivalent instruments in other countries, goes further. It can compel collection of data going forward and prohibit the company from disclosing that the order exists. A VPN provider under such an order continues advertising its no-log policy to new customers while complying with the collection requirement for targeted users.
What Happens When There Are No Central Servers
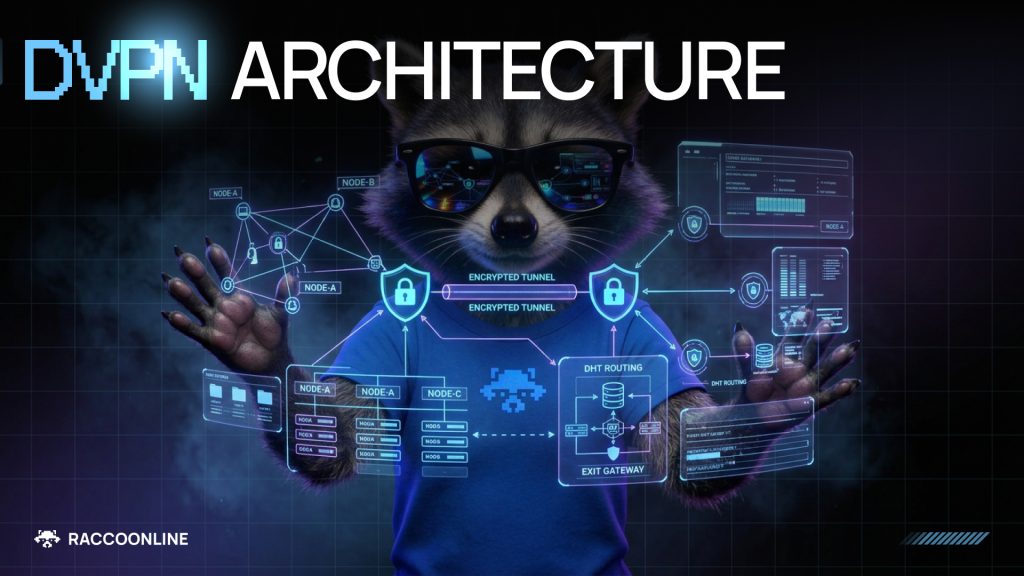
A decentralized VPN routes traffic through a network of independent node operators. Traffic is fragmented across multiple nodes in sequence. The entry node sees the user’s IP address and the next hop in the routing chain. The exit node sees the destination and the previous hop. No single node holds both the origin and destination of a connection.
A subpoena served on RaccoonLine as a company would produce no useful connection records, because RaccoonLine does not hold them. The routing information is distributed across independent node operators in different jurisdictions, none of whom hold a complete record.
Jurisdiction Stacking
Centralized VPN providers attempt to address legal pressure through jurisdiction selection. Incorporating in Panama, the British Virgin Islands, or other locations with weak data disclosure requirements reduces legal exposure from any single government.
This works until it does not. A company incorporated in a privacy-friendly jurisdiction still operates servers that may be physically located in other countries. Those servers are subject to the laws of their physical location. A P2P node network distributes nodes across dozens of countries simultaneously. There is no single physical location to target. Effective legal compulsion would require coordinated action across multiple jurisdictions, each with its own legal process and timeline.
Who This Matters For
For most VPN users, the subpoena scenario is theoretical. For journalists working with sensitive sources, activists operating in legally hostile environments, or anyone whose activity could attract legal attention from a well-resourced government actor, the structural distinction matters directly.
The question to ask when evaluating a VPN is not whether the company promises not to keep logs. The question is what happens when a government orders them to.
About RaccoonLine
RaccoonLine is built around the subpoena problem: the company holds no connection records linking users to their activity. Routing data is distributed across independent node operators in fragments that are useless without each other. A subpoena served on RaccoonLine produces nothing actionable. The product includes built-in decentralized file storage and clients for Windows, macOS, iOS, and Android. More information is available at raccoonline.com.
Contact
CMO
German Melnik
[email protected]

