Researchers at ThreatPress, WordPress’ security firm, confirm that several Multidot WordPress plugins bugs made e-commerce websites vulnerable to hacking. Ten WordPress plugins designed for e-commerce websites were disabled as the developers failed to release patches. These plugins were developed for sites powered by WooCommerce.
ThreatPress Identify Some Multidot WordPress Plugins As ‘Dangerous’
In a blog post on Thursday, ThreatPress highlighted ten different WordPress plugins designed specifically for e-Commerce websites as ‘dangerous’. All these plugins belonged to the same company MULTIDOTS Inc. According to the researchers, these plugins pose a severe threat to all online business websites powered by WooCommerce and using one of these plugins.
The researchers identified cross-site request forgery(CSRF), stored cross-site scripting (XSS), and SQL injection vulnerabilities, which any hacker could exploit to upload keyloggers, crypto-miners, shells, and other malicious software. In fact, they could even deface the websites entirely through these vulnerabilities.
An important thing to note here is that all these plugins focused explicitly on the WooCommerce sites of online stores. These websites can serve as a rich source of data to the hackers since they contain personal details of the customers along with their credit card details and other sensitive information. Therefore, securing these websites was a matter of great urgency.
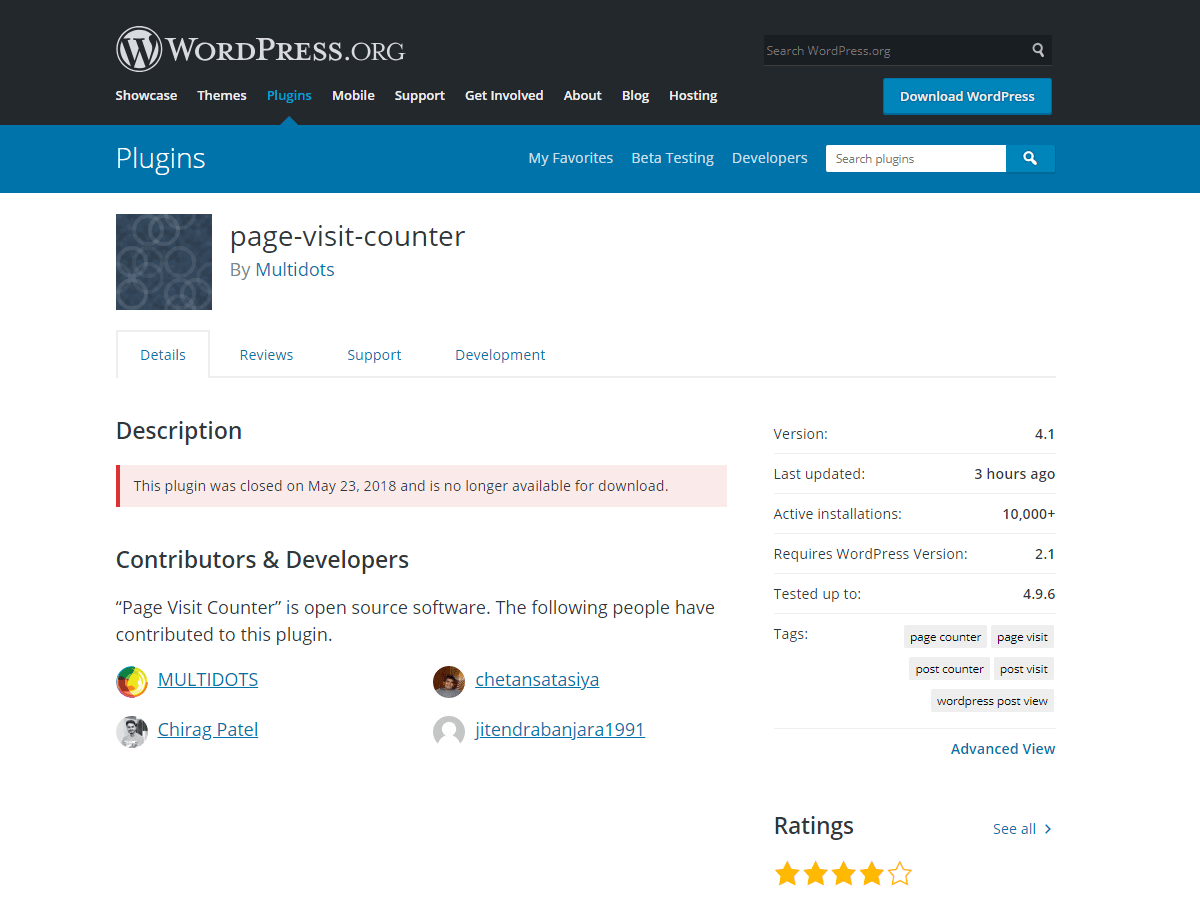
WordPress Closed All Faulty Multidot Plugins
ThreatPress notified Multidot Inc. about the vulnerabilities almost a month ago. However, the vendors did not take any serious steps to resolve the matter even after three weeks. ThreatPress eventually notified WordPress of the risks, after which WordPress disabled all ten faulty plugins.
According to ThreatPress they appreciated WordPress’ efficiency towards assuring the security of its users. Nonetheless, they expressed some concerns about the disclosure of this information to the customers.
“It is good to know that WordPress Security reacts quickly. But still, we’ve a big problem. There’s no way to inform all users of these plugins about the threat. It is strange that WordPress can show you information about available updates, but still can’t protect you by providing the information about closed plugins in the same way.”
The disabled plugins have almost 20,000 active installations. It means that proactive dissemination of this information can secure nearly 20,000 online stores from potential hackers.
Let us know your thoughts in the comments below.