East is a Python based security framework toolkit. It acts as a HTTP server and contains a wide range of different exploits and modules to use. It combines an advanced penetration testing framework with a simple to use interface, which even a beginner can use.
Installing EaST
Installation is pretty straightforward, clone the github repository.
git clone https://github.com/C0reL0ader/EaST.gi
It just requires python to run the server, nothing more.
Running EaST
Type this command to run the server.
cd East/
python start.py [-p PORT] [--all-interfaces]
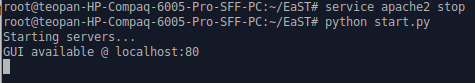
The service is up and running at localhost:80. Open a browser and go to the address.
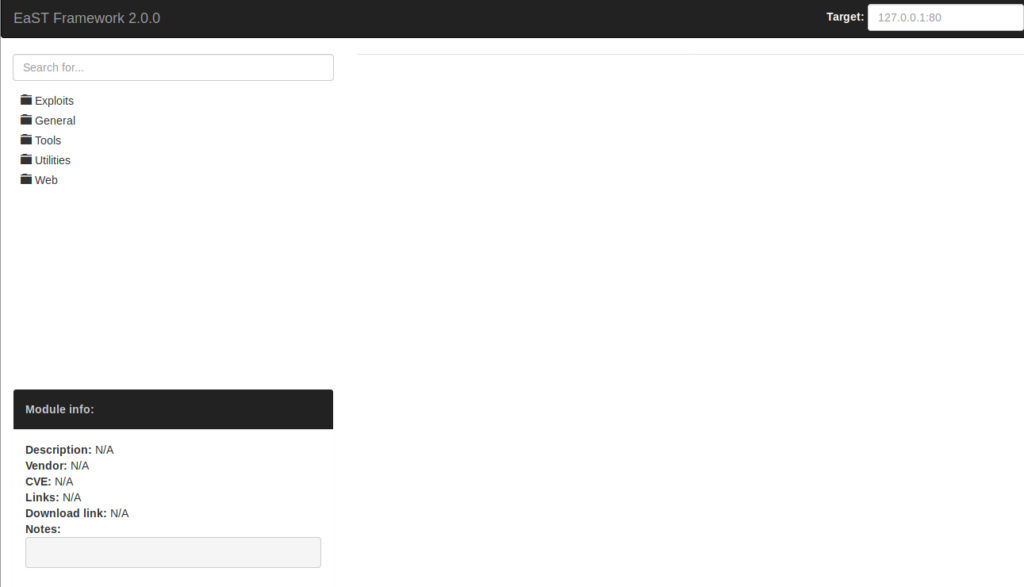
As you can see, the interface is pretty simple. In the left we have folders with modules we can use and also a window with information for every module you choose. In the right you have a box to type your target’s address and port you want to attack. You can also check their database with all the latest exploits here.
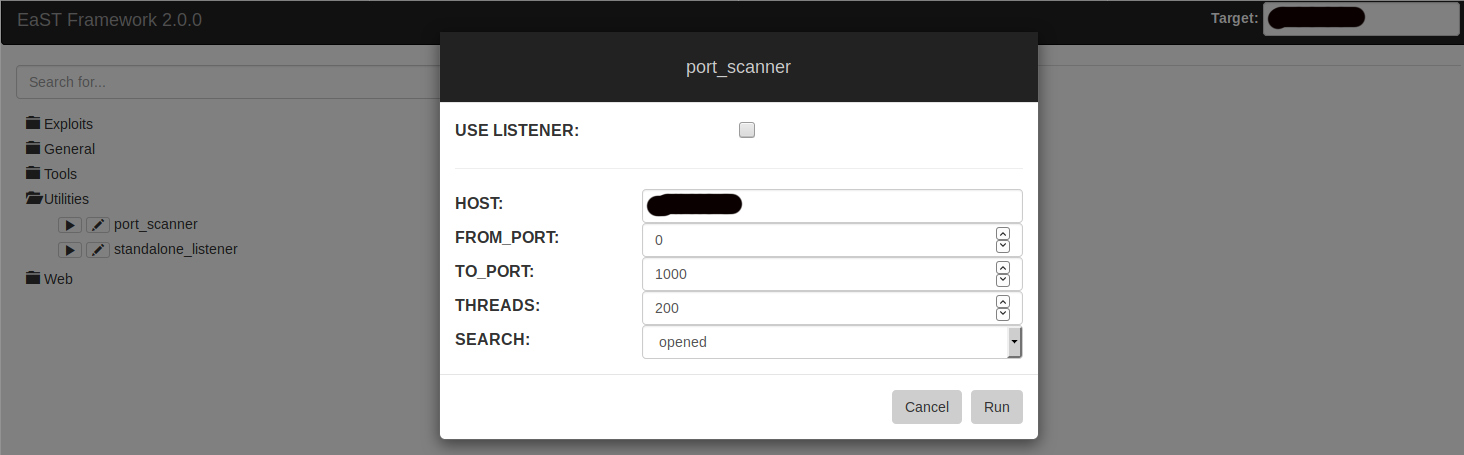
Let’s use it to attack a vulnerable server. First, type the target’s ip in the target box. Then, go to the Utilities folder and run the port_scanner module to see the open ports.
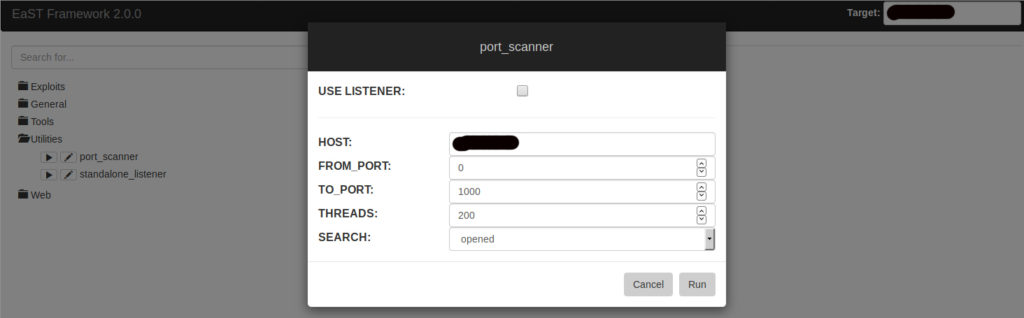
All you have to do after that is to check the available exploits and choose the right one for your target. From web to buffer overflows, there’s a good chance to find something interesting there.
What Bunny rating does it get?
EaST is a very good exploitation framework. You can learn and improve your IT knowledge in system attacks, improvement and protection. It easily gets a 4 out of 5 bunnies.
Want to learn more about ethical hacking?
We have a networking hacking course that is of a similar level to OSCP, get an exclusive discount here
Help support LHN by buying a T-shirt or a mug?
Check out our selection here
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.