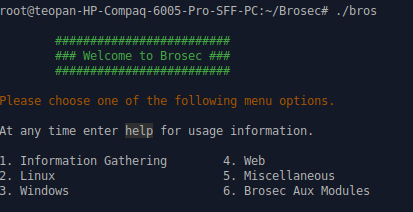
Brosec is an open source terminal based tool to help all the security professionals generate the right payloads and commands. It can show you all the most popular commands you can use for information gathering, Linux, Windows, web and utilize payloads.
Installing Brosec
Let’s clone the repository, first.
git clone https://github.com/gabemarshall/Brosec.git
After that install the missing dependencies.
apt-get install npm npm install
Now, you are good to go.
Running Brosec
To run brosec, execute the script inside the folder.
cd Brosec/ ./bros
As you can see below, the interface is easy to use, you just need to type the right option.
Let’s dig it a little. So, for example let’s say I have an exploit written in perl and I want to embed my own reverse payload. I type ‘5‘, and go to the reverse shell category to see all the examples. 
In another example, I’ve successfully exploited a Linux target and want to perform a Privilege Escalation attack. I type ‘2‘ and then go to the ‘Privesc‘ tab. I see some useful commands I can run against the target.

Brosec also has it’s own modules to choose between http ot ftp server. You can also encode various payloads, which it might be helpful to bypass basic security.

What Bunny rating does it get?
A very useful tool for security professionals. It’s a friendly companion for any red team exercise. It has many different options to choose between. We rate it 4 out of 5 bunnies.




Want to learn more about ethical hacking?
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

Comments are closed.