Google launched the Chrome 76 browser version amidst a lot of hype regarding its changes. The most important update with this browser release was the end of Incognito Mode tracking by websites, at least this is what Google claimed. However, it seems that their changes haven’t really gone to plan as websites have figured out alternate ways to detect Google Chrome Incognito Mode.
Chrome Incognito Mode Detection Continues
Google supposedly ended the option for websites to track users browsing in incognito mode by enabling the FileSystemAPI. Previously, websites used the absence of FileSystemAPI in incognito mode to detect private browsing on Chrome. So, enabling it in both browsing modes seemingly ended a way to track incognito mode.
However, it now seems that FileSystemAPI tracking was not the only method to track incognito browsing as multiple researchers have highlighted some other methods.
Method #1: Detecting Through Through Filesystem Quotas
This method highlighted by Vikas Mishra involves tracking the quota of temporary disk storage assigned to the Incognito window.
As explained by Mishra, there is a maximum limit of 120 MB for incognito mode. Whereas, for normal browsing window, there is no hard limit.
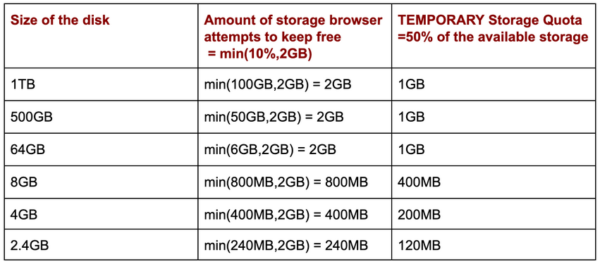
TEMPORARY storage has a default quota of 50% of the available disk as a shared pool for all the applications/websites.
Quota for an incognito window is a fraction (10%) of the device memory with an upper limit of 120MB.
He has explained these calculations in the following table.
Source: Vikas Mishra
Based on these calculations, he explained how one can detect incognito mode.
From the above table, it’s clear that for the temporary storage quota to be less than 120MB in case of non-incognito mode the device storage has to be less than 2.4GB. However, for all practical purposes, it is safe to assume that the majority of the devices currently in use have more than 2.4GB of storage.
This let him create a simple rule: if temporary storage quota <= 120MB, the user is in incognito mode.
Source: Vikas Mishra
Method #2: Detecting Through Access Timings
This method highlighted by the researcher Jesse Li involves tracking speed of FileSystemAPI writes. As stated in her blog post,
FileSystem API writes are measurably faster and less noisy in incognito mode, allowing websites to detect incognito visitors by benchmarking their write speed.
Li has also shared detailed source code for the PoC on GitHub for anyone to reproduce the results. While there are some limitations to the attack, Li states the technique is “harder to patch”.
However, as possible mitigation, Li advises using the same storage medium for both browsing modes. This will let the API run at the same speed.
While the websites have already switched to other ways to detect Incognito Mode, Google reiterated its plans to fix Incognito detection, as reported by BleepingComputer to whom Google commented that they plan to;
work to remedy any other current or future means of Incognito Mode detection
Let us know your thoughts in the comments.

