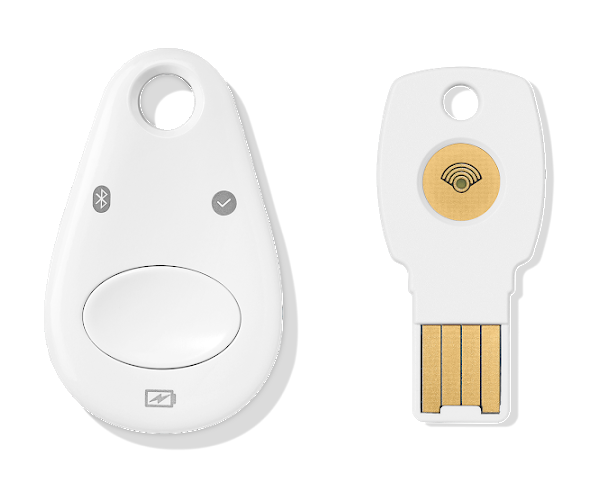
Hardware security keys are among the most robust account security tools of today. However, researchers have found how to clone these hardware security keys, thus risking the account security. Nonetheless, the overall attack has numerous limitations which still make using U2F security keys a better choice.
Clone Hardware Security Keys
Researchers from NinjaLab have found a way to clone hardware security keys threatening U2F security. As disclosed via their post, a side-channel attack can possibly allow an adversary to target the secure element in U2F-based hardware security keys and extract the encryption key.
Targeting the secure chip this way allows the attacker to make a clone of the security key. In turn, it lets the adversary break into the victims’ accounts.
Briefly, in their study, the researchers aimed at the Google Titan Security Key, targeting its NXP A700X chip. The chip basically implements ECDSA signatures as the core cryptography. Whereas, exploiting the electromagnetic radiations of the chip during the cryptographic process could possibly allow recovering the private key.
To understand the ECDSA engine, they took the help of Rhea (NXP J3D081 JavaCard smartcard) that implements the same cryptographic library.
Eventually, they could recover the private key from Rhea, and in turn, from Google Titan keys as well.
The vulnerability has received the identifier CVE-2021-3011. Whereas, regarding the vulnerable products, this attack affects many hardware security keys, which predominantly include the Google Titan Security Keys. Precisely, the list of vulnerable products includes the following,
- Google Titan Security Key (all versions)
- Yubico Yubikey Neo
- Feitian FIDO NFC USB-A / K9
- Feitian MultiPass FIDO / K13
- Feitian ePass FIDO USB-C / K21
- Feitian FIDO NFC USB-C / K40
- NXP J3D081_M59_DF and variants
- NXP J3A081 and variants
- NXP J2E081_M64 and variants
- NXP J3D145_M59 and variants
- NXP J3D081_M59 and variants
- NXP J3E145_M64 and variants
- NXP J3E081_M64_DF and variants
Attack Limitations Make It Less Likely
While the attack sounds almost perfect to extract private keys and ruin the security of U2F authentication, it isn’t feasible for real-time attacks due to several limitations.
The main limitation here is that the attacker should have explicit and prolonged physical access to the target security key to clone it.
Besides, the overall experimental setup is quite expensive to afford for an average attacker.
Nonetheless, for the most determined adversaries, executing such attacks isn’t entirely impossible.
Therefore, the researchers advise the users to switch to the more secure hardware security keys.
However, they still recommend using these security keys (including Google Titan) to protect accounts instead of not using any.
The researchers have presented their findings in detail in their report here.

1 comment
This kind of work pleases me very much.
Comments are closed.