Dalfox is a fast, powerful parameter analysis and XSS scanner based on a DOM parser. Other than finding XSS it also has additional features that test for sqli,ssti,open-redirects. It is capable of finding reflected, stored, and blind XSS.
Dalfox Installation
There are numerous ways to install the package, one of which being via Homebrew.
Installing using Snapcraft
This method of installation requires snapcraft to be installed. You can find out if the snap is installed in your system by using the snap command, if it is not installed you can follow this link to install snap in your system.
sudo snap install dalfox
The next two methods, require the latest go version install in your system. You can check the install version by using the command go version if go is not installed you can follow this link to install the go.
Installing from source
GO111MODULE=on go get -v github.com/hahwul/dalfox/v2
Installing using GitHub
git clone https://github.com/hahwul/dalfox cd dalfox go build .
Installing using docker
docker pull hahwul/dalfox:latest
You can run using this command: docker run -it hahwul/dalfox:latest /app/dalfox url https://www.hahwul.com
The below method only works on the macOS.
Install using Homebrew
brew tap hahwul/dalfox brew install dalfox
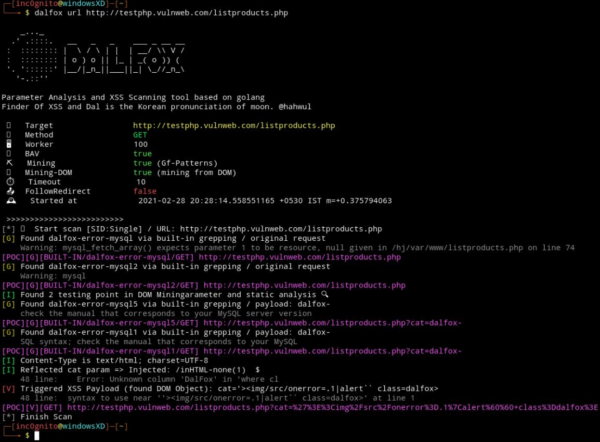
How Dalfox Works
Scanning a single URL
dalfox url http://testphp.vulnweb.com/listproducts.php
Scanning multiple URL
Dalfox can also scan multiple URLs.
cat samples/sample_target.txt | dalfox pipe OR dalfox file ./samples/sample_target.txt
You can use paramspider to find the parameter and then pass multiple URLs to Dalfox to get better results.
What Bunny rating does it get?
It is a fast tool to find XSS and other commons web vulnerabilities, The tool gives very few false positives and has additional features to find sqli, ssti and many more things. we will be awarding this tool a rating of 4.5 out of 5 bunnies.




![]()
Want to learn more about ethical hacking?
We have a networking hacking course that is of a similar level to OSCP, get an exclusive 95% discount HERE
Do you know of another GitHub related hacking tool?
Get in touch with us via the contact form if you would like us to look at any other GitHub ethical hacking tools.

