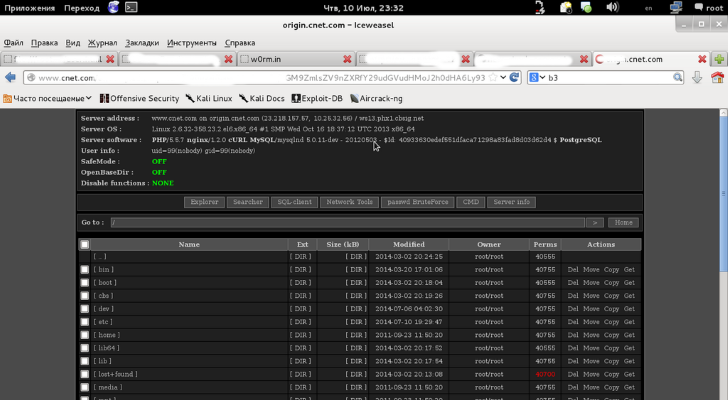
The data stolen from CNET’s servers is said to contain usernames, emails and encrypted passwords, and the group, communicating under the alias “w0rm,” tweeted that they were willing to sell the information for as little as one Bitcoin (roughly $620/€455).
Perpetrators said they asked for such a low price because they wanted to gain notoriety. The security hole exploited is in the Symphony PHP framework, which allows web developers to build more sophisticated websites.
A representative from CBS Interactive, which owns the CNET publication, admitted the servers had been accessed by an attacker over the weekend and said that the issue had been identified and eliminated, but they would keep their eyes on the matter.
W0rm did not provide the full path to the exploit, and it appears that the motivation behind the attack was to raise security awareness, a high-profile website being the best way to achieve this goal.
The passwords retrieved by the hackers are encrypted, there is no information on the algorithm used to protect them or if they were salted and hashed.
As a precaution, it would be wise for those with login credentials for CNET website to change their passcodes for the service, even if decrypting the details may not lead to accessing them in plain text.