Google app phishing flaw discovered by two security researchers; Patrik Fehrenbach and Behrouz Sadeghipour have discovered a vulnerability in Google Apps which enabled cyber criminals to register a corporate domain and the send non-blocked phishing emails from admin email addresses.
The Choc Factory have since patched the flaw and awarded the US$500 to the researchers as a bounty.
the vulnerability allowed attackers to register the name of a company that had not yet signed up to Google Apps for Work, they could then send phishing emails to staff, making it appear to come from a legitimate corporate domain. This also meant that spam filters were not tripped.
Google have since patched the vulnerability by altering the received email address from admin to [email protected].
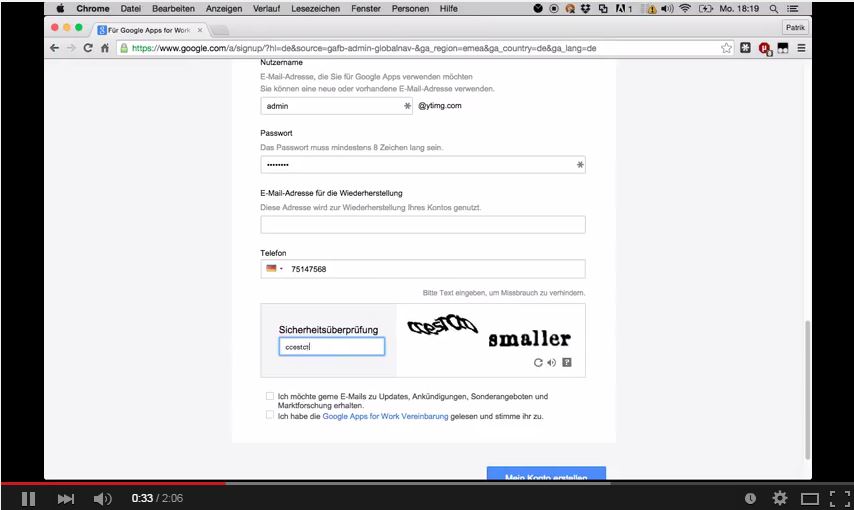
See the video below for details of how the flaw worked: