Microsoft has patched a security flaw in the Windows Print Spooler service that allows hackers to take over devices through a simple mechanism. Security firm Vectra discovered the vulnerability (CVE-2016-3238), this vulnerability affects all Windows versions ever released. This vulnerability was then fixed by Microsoft in MS16-087. The flaw could allow an attacker to install malware remotely on victim machine that can be used to view, modify or delete data, or create new accounts with full user rights, according to MS16-087 bulletin by Microsoft.
Usually in corporate networks admins allow printers to deliver the necessary drivers to workstations connected to the network. These drivers are silently installed without any user interaction and run under the SYSTEM user with all the available privileges.
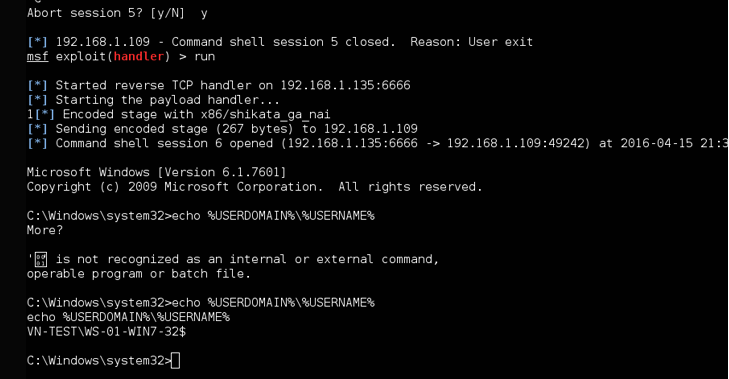
An attacker can replace these drivers on the printer with malicious files that allow them to execute any code they’d like on the infected machine, according to Vectra researchers.
Other Possible Attacks Through This Vulnerability :
- The attack can also be launched from the local network or via the Internet and these type of attack can be delivered via innocuous methods such as ads (malvertising) or JavaScript code hidden in compromised websites.
- If the printer is behind a firewall then the attackers can even hack other device or computer on that particular network, and then use it to host their malicious files.
Watering Hole Attacks via Printers
Watering hole attacks are used to target businesses and organizations by infecting them with malware to gain access to the network. Like servers, several computers are also connected to printers in an effort to print documents as well as download drivers. So this flaw allows a hacker to execute watering hole attacks technically using printers.
“Rather than infecting users individually, an attacker can effectively turn one printer into a watering hole that will infect every Windows device that touches it,” said Vectra chief security officer Gunter Ollmann.
This flaw (CVE-2016-3238) which is easy to execute and plus provides different ways of launch attacks making it more easy for the hackers also a huge number of users can be attacked. As far as this year this flaw is the most dangerous vulnerability.