Dracos Linux ( www.dracos-linux.org ) is the Linux open source operating system and built based on the Linux From Scratch under the protection of the GNU General Public License v3.0. This operating system is one variant of Linux distributions, which is used to perform security testing (penetration testing). Dracos linux in Arm by hundreds hydraulic pentest, forensics and reverse engineering. Does not use a GUI-based tools-tools and just have the software using the CLI (command line interface) to perform its operations. Now Dracos currently already up to version 2.0 with the code name “Leak“.
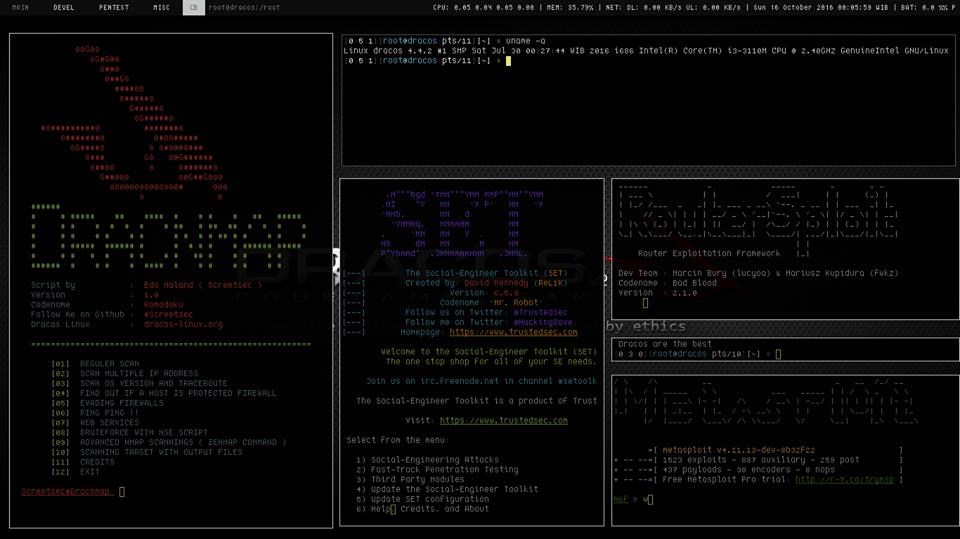
Screenshot:
Video:
Note: Dracos Linux is purposed as an educational,especially to recognize the operation system of linux and we respect ethical hacking.
Build from source codes instead of installer, this will stimulate users in Indonesia to stay creative and to build the spirit of opensource. Dracos Linux intends to construct the repository to build up the processes Like Venomizer. Dracos in build from source code, thus forcing us to compile when installing a package or software, which of course will arise the possibility of system failure and other system vulnerabilities.
Always from terminal
None of every singel tool that was installed inside the OS uses GUI. CLI will always consider to particularly openbox to ease the users in need of multi terminal in applying Penetration Testing
Penetration Tools List:
Link : http://dev.dracos-linux.org/projects/dracoslinux/wiki/Penetration_Testing
- Information Gathering
- Vulnerability Assessment
- Web Attack
- Exploitation Testing
- Privilege Escalation
- Password Attack
- Social Engineering
- Man In The Middle Attack
- Stress Testing
- Wireless Attack
- Maintaining Access
- Forensics Tools
- Reverse Engineering
Malware Analysis - Covering Track