Today in this tutorial we will have a look at how we can use Nmap (Which stands for Network Mapper )in Kali Linux to scan for open ports. To do this, we will use OS detection.
Nmap is an open source tool that can be used for network exploration and security auditing. This comes standard with Kali Linux but is also available for users with other operating systems like OSX, Windows and also many UNIX platforms. If you are interested use to Nmap with a GUI, you can opt for Zenmap, which is a graphical interface for the Nmap.
First I want to start off with a little warning: Please be careful using the more aggressive functions of Nmap against hosts you do not own or do not have permission to scan. It may be against your ISP’s terms to use some Nmap features.
Open Port Scanning and OS Detection
Let’s start with a ping scan on an IP range to determine live hosts using the following command:
nmap -sP 192.168.0.0-100
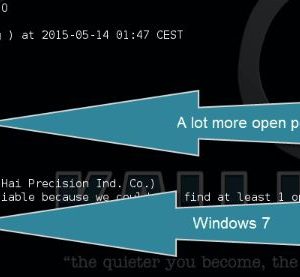
Next we will start a SYN scan with OS detection on one of the live hosts using the following command:
nmap -sS [ip address]-O
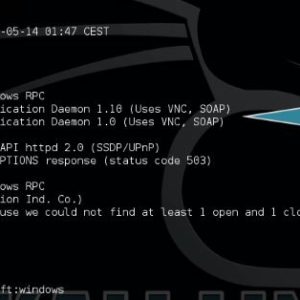
Now we will start an open port scan with version detection using the following command:
nmap -sV 192.168.0.1 -A
When we add -v to the command we can increase the verbosity :
nmap -sV 192.168.0.13 -A -v